North Korea's $800M Crypto War Chest: Treasury Busts the Network Funding Kim's Missiles

US Treasury sanctioned 6 individuals and 2 companies on March 13, 2026 for laundering $800 million in crypto for the DPRK regime. (BLACKWIRE / nixus.pro)
The US Treasury Department dropped sanctions on 6 people and 2 shell companies Friday for running the crypto laundromat that funnels stolen digital assets back into Pyongyang's weapons development machine. The operation laundered $800 million in crypto proceeds - money that the DPRK's Lazarus Group extracted from global exchanges, DeFi protocols, and crypto firms through sophisticated cyberattacks.
This isn't a peripheral enforcement action. It is a snapshot of how Kim Jong-un's regime finances intercontinental ballistic missile tests, nuclear warhead miniaturization research, and the surveillance apparatus that keeps 25 million North Koreans locked inside one of the world's most closed societies. Stolen crypto paid for it. And for years, the operation ran quietly through proxy companies, Chinese over-the-counter desks, and covert IT workers embedded inside legitimate Western technology firms.
Treasury's Office of Foreign Assets Control (OFAC) said the sanctioned individuals and companies helped channel North Korean IT wages and hacking proceeds back to Pyongyang, evading international sanctions that were already supposed to be choking the regime's financial lifelines. The action comes 13 days into a new Iran conflict that has markets on edge and geopolitical risk premiums at multi-year highs.
Treasury Action - March 13, 2026
The IT Worker Gambit: How Pyongyang Placed Agents Inside US Tech
North Korea's most audacious financial operation isn't a hack. It's a hiring scam. For at least four years, the DPRK has systematically placed thousands of covert IT workers inside legitimate technology companies around the world, including firms headquartered in the United States. These workers use fake identities, forge LinkedIn profiles, fabricate GitHub portfolios, and take remote freelance and full-time developer positions that pay real salaries in real dollars.
The wages - often between $60,000 and $120,000 per year for experienced developers - flow through a network of bank accounts and crypto wallets before reaching facilitators who convert the funds into untraceable assets and route them back to Pyongyang. Treasury estimates that each worker generates tens of thousands of dollars per year for the regime. With thousands of workers active simultaneously, the aggregate annual haul from this program alone runs into hundreds of millions of dollars.
The DOJ and FBI have been tracking these networks since at least 2022. In a series of indictments, US authorities described North Korean nationals working under assumed identities for companies ranging from small startups to Fortune 500 contractors. They use US-based "laptop farms" - physical locations where local enablers receive workers' computers and operate them to mask the actual foreign location - to pass remote work verification checks and fool IP-based geo-detection systems.
"The DPRK has dispatched thousands of highly skilled IT workers around the world to generate revenue that contributes to its unlawful WMD and ballistic missile programs." - US Treasury Department statement, March 13, 2026
The sanctioned companies appear to have operated as facilitators in this pipeline - entities that helped move the resulting wage proceeds through layers of financial obfuscation before the money could be consolidated and sent to Pyongyang's handlers. These are not simply passive financial institutions. They are active co-conspirators in the scheme, according to the OFAC designation.
For crypto compliance teams, the IT worker threat represents a different challenge than exchange hacks or protocol exploits. The money enters the system clean - it looks like normal payroll. The obfuscation happens downstream. By the time anyone asks questions, the trail runs through multiple wallets, mixer contracts, cross-chain bridges, and OTC desks across jurisdictions that don't cooperate with US financial regulators.
The Lazarus Group's $3.6 Billion Crypto Empire
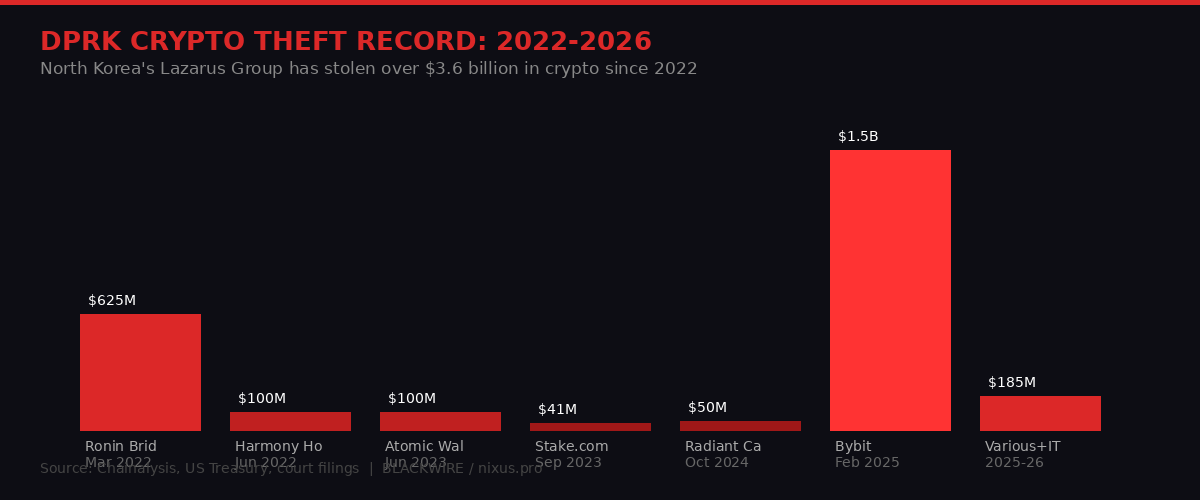
North Korea's Lazarus Group has stolen over $3.6 billion in cryptocurrency since the 2022 Ronin Bridge hack. The Bybit exploit in February 2025 remains the largest single crypto theft in history. (BLACKWIRE infographic / nixus.pro)
The $800 million laundering network dismantled Friday is downstream of a much larger operation. The Lazarus Group - the DPRK's elite state-sponsored hacking unit, operating under the Reconnaissance General Bureau - has stolen an estimated $3.6 billion or more in cryptocurrency since 2022 alone, according to Chainalysis blockchain analytics data.
The list of Lazarus attacks reads like a greatest-hits album of the crypto industry's worst nightmares:
- Ronin Bridge, March 2022: $625 million stolen from the Axie Infinity sidechain. The FBI attributed the attack to Lazarus within weeks. Recovery of even a fraction took years of law enforcement coordination.
- Harmony Horizon Bridge, June 2022: $100 million extracted via a multi-signature wallet compromise. North Korean operatives spent over a year slowly laundering these funds through Tornado Cash.
- Atomic Wallet, June 2023: $100 million in user funds vanished across more than 5,500 individual wallets in a breach that targeted non-custodial wallet holders directly.
- Stake.com, September 2023: $41 million from the crypto gambling platform, extracted in under 90 minutes across three separate blockchains.
- Radiant Capital, October 2024: $50 million in a sophisticated attack on a cross-chain lending protocol - attackers compromised multiple developer machines to achieve the necessary multi-sig threshold for an unauthorized upgrade.
- Bybit, February 2025: $1.5 billion - the single largest crypto theft in history, period. Lazarus compromised Bybit's cold storage infrastructure via a sophisticated supply chain attack on Safe{Wallet} signing infrastructure. The theft wiped out the equivalent of approximately 400,000 ETH in a single transaction sequence.
The Bybit hack alone dwarfs the total value of today's $800 million laundry operation. It underscores the scale of what Pyongyang is working with. The regime doesn't need to run tight margins on laundering - it has such a volume of stolen assets that even a 20-30% haircut on conversion costs is acceptable. The treasury ends up replenished regardless.
Chainalysis noted in its 2025 Crypto Crime Report that North Korea-linked entities accounted for more than 60% of all crypto stolen by state-sponsored actors globally. No other nation-state program comes close.
How $800 Million Gets From Blockchain to Ballistic Missiles

The DPRK laundering pipeline typically runs: exchange hack or IT wages - chain-hop - mixer - OTC desk - fiat conversion - into regime coffers. Each step adds obfuscation. (BLACKWIRE infographic / nixus.pro)
Understanding how crypto converts into weapons budget requires understanding the full pipeline. It is not a simple bank wire. The process involves multiple layers specifically designed to defeat blockchain analytics, break regulatory reporting chains, and emerge as clean fiat currency - or hard assets - in jurisdictions that won't cooperate with US law enforcement.
Step 1 - Theft or wage generation. Funds enter the pipeline either through a direct hack (Lazarus exploits a protocol, bridge, or exchange) or through IT worker wages being paid into accounts controlled by DPRK facilitators. Both paths create crypto balances in wallets that, at this stage, can be directly linked to North Korean activity.
Step 2 - Chain hopping. The crypto is immediately moved across multiple blockchains using cross-chain bridges. Moving from Ethereum to Bitcoin to Tron to BNB Chain in rapid succession creates multiple transaction records across separate blockchains, none of which are natively interoperable. Blockchain analysts must manually reconstruct the trail.
Step 3 - Mixing. Coin mixers and privacy protocols - Tornado Cash was the primary vehicle until it was sanctioned by Treasury in August 2022 - are used to break the on-chain link between source and destination wallets. Despite Tornado Cash's sanctioning and the arrest of its developer, alternative mixing infrastructure continues to operate. North Korean operatives have been documented using multiple mixer alternatives post-Tornado.
Step 4 - OTC conversion. The "cleaned" crypto moves to over-the-counter desks, predominantly operating out of China and Southeast Asia, that exchange large crypto volumes for fiat currency or other assets without filing the suspicious activity reports required of licensed exchanges. These desks accept the compliance risk in exchange for spreads that can run 3-5% on large volumes - meaning they take tens of millions in fees for facilitating billion-dollar flows.
Step 5 - Fiat movement and final delivery. The converted fiat moves through hawala networks, Chinese bank accounts with weak AML enforcement, and front companies before reaching DPRK handlers who deliver the funds to regime-controlled institutions. The UN Panel of Experts on North Korea has documented this final-mile process extensively in its annual sanctions monitoring reports.
The two companies sanctioned Friday operated somewhere in steps 3-5. By cutting off these nodes, Treasury makes it incrementally harder and more expensive for Pyongyang to convert its next haul. But the network reconstitutes. Sanctioned OTC operators simply pass books to new entities, re-incorporate under new names, and restart.
Friday's Market Context: Bitcoin, Iran, and the Geopolitical Premium
The Treasury action landed on an already turbulent Friday. Bitcoin surged to a near one-month high of $74,000 during the US morning session as traders rotated from gold and equities into crypto on hopes of a ceasefire or diplomatic resolution to the 13-day-old Iran conflict. The CoinDesk 20 index jumped 3.7%. Sui gained 6.7%, Cardano 5.8%, XRP broke above $1.39 on a 300% volume surge.
Then, around 4:30 PM Eastern time, everything reversed.
US Central Command confirmed that all six crew members aboard a refueling aircraft that crashed in Iraq on Thursday had died - the single largest US military casualty event since the conflict began. Simultaneously, the Wall Street Journal reported that the Pentagon was deploying a Marine Expeditionary Unit of approximately 2,500 troops to the region, with forces attached to the USS Tripoli, as Iran stepped up attacks around the Strait of Hormuz.
Bitcoin dropped 3.5% in under 30 minutes - from $74,000 to just above $71,200. The S&P 500 and Nasdaq reversed early gains to finish down 0.4%-0.5%. Oil reversed a session decline to trade up nearly 2% at $97.30 per barrel. Gold, bizarrely, continued lower despite the geopolitical flare-up - down another 1% as dollar strength weighed.
"Optimism over geopolitical events, including Russian sanction relief, has been a driver. These headlines tend to have a short half-life, so we would expect this to be short-lived till we see concrete follow-up action." - Paul Howard, Director, Wincent trading firm (CoinDesk)
The North Korea sanctions action adds a third geopolitical thread to a market already processing Iran military escalation and ongoing Russia-Ukraine normalization talks. For crypto specifically, DPRK sanctions have historically had muted direct market impact - the 2022 Tornado Cash action caused a few days of NFT and DeFi selling but no sustained trend. This action targets facilitators, not the protocols themselves, and is unlikely to cause immediate price disruption.
The indirect effect is more interesting: every Treasury enforcement action tightens KYC requirements across the industry, accelerates the compliance costs for exchanges and OTC desks, and nudges institutional money toward regulated venues with stronger AML frameworks. This benefits Coinbase, Circle, and licensed custody providers at the expense of offshore alternatives.
The Bybit Aftermath: $1.5 Billion Still Being Laundered
Friday's action is also significant in the context of the Bybit hack from February 2025. Lazarus extracted $1.5 billion in ETH-related assets from Bybit's cold storage infrastructure in what blockchain forensics firm Elliptic called "the most sophisticated cryptocurrency theft ever executed." More than a year later, a substantial portion of that money remains in various stages of the laundering pipeline.
Chainalysis tracked the Bybit funds through an elaborate web of chain hops and mixer interactions in the weeks following the theft. North Korean operatives moved funds in tranches, using different wallet clusters for different asset types, and deliberately slowing the pace of conversion to avoid triggering exchange alerts. Some portion was converted through the same types of OTC networks that Treasury targeted Friday.
Bybit CEO Ben Zhou said publicly that the exchange would replenish client losses - and did, raising emergency funding from VCs and crypto funds within days. But the laundering machine continues operating. Treasury's action disrupts some of the pipeline but doesn't recover funds. No enforcement action has ever successfully clawed back a significant portion of DPRK-stolen crypto. The closest analogy is the 2022 Colonial Pipeline ransomware case, where DOJ recovered approximately $2.3 million in Bitcoin - about half the ransom - by seizing a wallet belonging to the criminal infrastructure. DPRK operations are orders of magnitude more sophisticated than ransomware groups.
The Bybit hack specifically exploited a blind trust in Safe{Wallet}, a widely-used multi-signature wallet infrastructure. Attackers compromised a developer's machine and injected malicious code into the front-end interface that Bybit's operations team used to authorize transactions - making a malicious transfer look identical to a routine internal transfer on their screens. By the time the fraud was detected, 400,000 ETH was gone.
The Stablecoin Angle: USDC, USDT, and North Korean Flows
Friday also brought a structural stablecoin milestone that connects directly to the enforcement story. For the first time since 2019, Circle's USDC recorded higher daily trading volumes than Tether's USDT, according to data cited by CoinDesk. Japanese investment bank Mizuho raised its Circle price target to $120 from $100 following the news.
This matters for North Korean sanctions enforcement because the two stablecoins represent fundamentally different compliance postures. Circle has consistently cooperated with OFAC, freezing wallets within hours of being notified of sanctions designations. Tether has historically been slower and less transparent about its compliance process, though it has improved in recent years. Chainalysis data has shown that USDT on Tron - the specific stablecoin/blockchain pairing favored by DPRK facilitators and OTC desks operating in China and Southeast Asia - accounts for a disproportionate share of illicit flows by stablecoin type.
A shift in market share from USDT toward USDC doesn't directly crimp North Korean operations tomorrow. Tron-based USDT remains the dominant medium for OTC conversion across Asian illicit networks. But the trend line matters: as institutional volumes move toward USDC, the compliance norms embedded in Circle's operating model become the industry standard rather than the exception. Over a multi-year horizon, that constrains the operating environment for DPRK facilitators.
Stanley Druckenmiller, the billionaire macro investor and former Soros fund manager, said Friday that stablecoins could "become the whole payment system" in 10-15 years and reiterated that Bitcoin might eventually displace the US dollar as the global reserve currency. If that trajectory materializes, the compliance and enforcement architecture built into dominant stablecoins becomes critically important for national security - not just financial regulation.
Stablecoin Market - March 13, 2026
What Happens Next: Enforcement, Escalation, and the DPRK Crypto Cycle
Treasury sanctions don't end the DPRK crypto program. They impose costs, slow specific pipelines, and signal political intent. The question is whether Friday's action is a one-off or the opening of a sustained enforcement campaign timed to the current geopolitical environment.
The context suggests the latter. The US is 13 days into a shooting war with Iran, dealing with elevated oil prices, a Marine deployment to the Gulf, and simultaneous pressure on Russia over Ukraine. In this environment, the last thing the administration wants is photographic evidence that North Korean crypto hackers are operating with impunity on US soil - which is essentially what the IT worker scandal represents.
The enforcement calendar also suggests more to come. The DOJ has active grand jury investigations into multiple DPRK-linked crypto operations. FBI's Virtual Asset Unit has been working DPRK attribution cases since at least the Ronin Bridge hack. Treasury's OFAC typically bundles related designations - Friday's action likely represents only a fraction of the sanctioned network that investigators have already mapped.
For the broader crypto market, North Korean enforcement creates a persistent regulatory overhang. Every major DPRK hack that makes headlines gives ammunition to legislators who want stricter KYC requirements for DeFi protocols, mandatory on-chain analytics integration, and liability frameworks that put developers in the crosshairs when their protocols are used for sanctions evasion. The Senate's GENIUS Act - the stablecoin regulatory framework that passed committee in late February - specifically includes provisions targeting sanctions compliance that were drafted with DPRK flows in mind.
The timeline of DPRK crypto enforcement shows that Treasury action accelerates after each major theft and then quiets during periods of diplomatic engagement. The current period - active Iran conflict, no active North Korea diplomacy - is maximum enforcement season. Expect more designations in the coming weeks.
Who Gets Hurt: The DeFi Protocols Caught in the Crossfire
When the Treasury sanctions hammer falls, the collateral damage usually lands on protocols that had nothing to do with enabling the theft - but whose architecture made them useful for obfuscation. That's the Tornado Cash lesson. The mixer's developer is serving time. The protocol still processes transactions on-chain because smart contracts cannot be turned off.
In the aftermath of North Korea attribution, several categories of crypto infrastructure face elevated regulatory scrutiny. Cross-chain bridges top the list. Four of North Korea's six largest heists specifically targeted bridge infrastructure - Ronin, Harmony Horizon, and multiple smaller bridges. The technical reason is simple: bridge validators and multi-signature threshold schemes are complex, often holding concentrated value with comparatively weaker security assumptions than layer-1 protocols. Lazarus has proven it can compromise the human layer - developer machines, multi-sig keyholders, internal tooling - even when the smart contracts themselves are clean.
Privacy protocols face the second wave of scrutiny. With Tornado Cash neutered and its developer convicted, North Korean operatives shifted to alternatives: Railgun, TornadoCash forks on other chains, and privacy-by-default layer-1 blockchains like Monero. Railgun's team has publicly said it does filtering to exclude known sanctioned wallets - but the technical challenge of preventing determined state-level adversaries from using your protocol is not solved by a blocklist. Monero remains essentially unlaundering to blockchain analytics firms - a fact that has made it a consistent Treasury concern.
OTC desks face the sharpest near-term operational risk. The two companies sanctioned Friday are almost certainly OTC or conversion facilitators. Being on the OFAC SDN list makes them untouchable for any US-connected counterparty - including the majority of major crypto exchanges, which maintain US banking relationships and cannot risk facilitating transactions with SDN-listed entities. The sanctioned firms will attempt to reconstitute under new names, but their existing counterparty relationships are severed.
For developers, traders, and market participants, the underlying message from Friday's action is consistent with everything Treasury has done since 2022: the free-for-all era of crypto as a sanctions-blind financial system is over. The US government can identify, attribute, and sanction crypto-based financial crime at scale. The gap between crypto operating norms and regulatory expectations is closing - faster than most of the industry anticipated three years ago.
The bottom line: $800 million laundered, 6 sanctioned, 2 companies blacklisted. North Korea's crypto machine took a hit Friday. It will rebuild. The regime has billions more in the pipeline from the Bybit haul alone. But every enforcement action raises the cost, tightens the network, and makes the next conversion harder. Pyongyang is playing a long game. So is Treasury.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram