Iran's Cyber Army Opens a Second Front: Hospitals, Power Grids and Water Plants in the Crosshairs
Day 13 of the Iran war. A Michigan medical device giant has been breached. Cameras across the Middle East have been hijacked for missile targeting. A Polish nuclear research facility has been compromised. Pro-Iranian hackers are moving toward US critical infrastructure - and the people who defend it say the gloves are finally off.
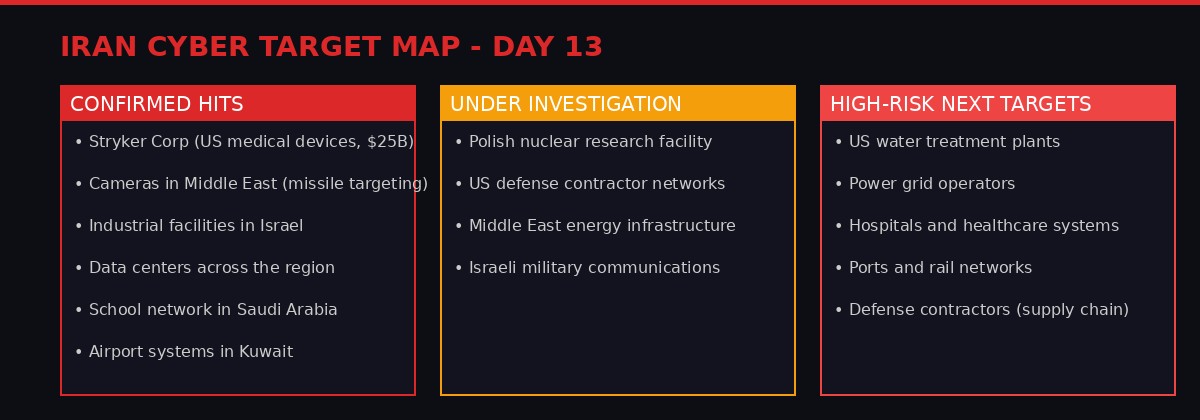
Iran's confirmed cyber hits and high-risk next targets as of Day 13. Graphic: BLACKWIRE
Stryker Corporation, a $25 billion US medical device company with 56,000 employees worldwide, confirmed Wednesday that pro-Iranian hackers breached its global networks. The Handala hacking group's logo appeared on company login pages. Stryker filed an 8-K with the SEC acknowledging the full scope and restoration timeline remain unknown. AP, WSJ, SEC
When Iran's war machine launched its opening salvo on February 28 - barrages of ballistic missiles that killed hundreds in Israel and drew US carrier groups into the Persian Gulf - most attention fixed on the kinetic: the fires over Tehran, the tankers burning in the Strait of Hormuz, the oil price shock that drove crude through $100 a barrel. What received less coverage was the simultaneous activation of Iran's second military: its cyber corps, operating in the dark, prepositioned inside American and allied networks, waiting for exactly this moment.
That second army has now moved. The attack on Stryker on March 12 - Day 13 of the conflict - is the most visible signal yet that Iran has opened a digital front against the United States directly. But intelligence analysts and cybersecurity researchers say Stryker is not the ceiling. It is the floor.
The Stryker Strike: What Actually Happened
Stryker Corporation is not a household name, but it is woven deep into the American healthcare system. Based in Portage, Michigan, the company makes artificial joints, surgical robots, hospital beds, trauma implants, and the kind of specialized equipment that keeps operating rooms running. Its 2025 revenue exceeded $25 billion. Its supply chains touch virtually every major hospital in the United States. Stryker SEC 8-K, March 12
On Wednesday, the company's Microsoft systems went dark. Login pages across its global network began displaying the logo of Handala, a hacking group with documented ties to Iran and the Palestinian cause. Stryker issued a public statement saying it had "no indication of ransomware or malware" and believed the incident was "contained" - but in the same breath filed an 8-K with the Securities and Exchange Commission acknowledging that the full scope of the attack and the timeline for restoration were both unknown. AP
Those two statements - "contained" and "scope unknown" - are contradictory. Security researchers note that companies often issue reassuring statements before their forensics teams have completed their work. The SEC filing is the honest document.
"Attacking a high-profile US health care manufacturer is exactly the kind of pressure point that creates outsized strategic and political ripple effects."
- Alexander Leslie, Senior Adviser, Recorded Future
Handala said explicitly that the attack was retaliation for US strikes that killed Iranian schoolchildren. The February 28 missile strike on Shajareh Tayyebeh Elementary School in Minab, which killed more than 165 people - many of them children - used outdated Defense Intelligence Agency coordinates, according to a preliminary US military investigation reported by AP and the New York Times. Iran's regime has used the strike as a propaganda cornerstone, and pro-Iranian hacking groups have weaponized it as justification for escalating attacks on American civilian targets. AP
Who Is Handala - and Why They Are Different
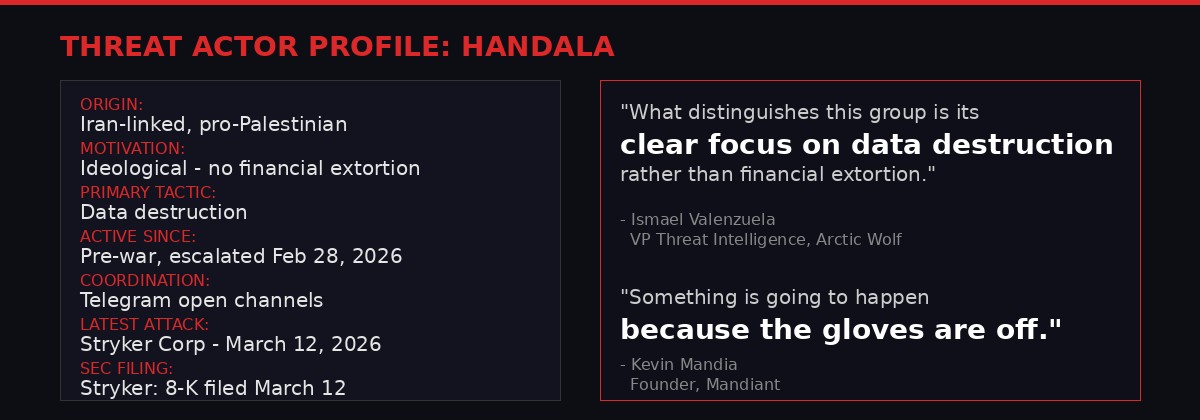
Key characteristics of the Handala group. Graphic: BLACKWIRE
Handala is not a ransomware crew. It is not trying to extract money. That distinction matters enormously when assessing the risk it poses to American infrastructure.
Most cybercriminal groups that breach corporate networks are ultimately rational economic actors. They encrypt data, demand payment, negotiate, and eventually provide decryption keys when money moves. There is a strange predictability to the relationship. Handala operates on a completely different logic.
"What distinguishes this group is its clear focus on data destruction rather than financial extortion."
- Ismael Valenzuela, VP Threat Intelligence, Arctic Wolf
Handala's goal is to destroy, disrupt, and humiliate. In the context of a hot war - where every day the United States is conducting airstrikes against Iran - that ideological motivation translates into a willingness to cause maximum damage to American economic life without any exit ramp. There are no negotiations with a group that wants your hospital's records wiped and your manufacturing systems permanently offline.
HANDALA - QUICK PROFILE
Active since at least 2023. Iran-linked, ideologically pro-Palestinian. Known for defacements, data dumps, and destructive intrusions. Claimed credit for attacks on Israeli systems in 2024 before pivoting to US targets as the Iran war escalated. Communicates openly via Telegram. Not known to pursue ransomware payments. Classed by Western intelligence as a "hacktivist" group with state adjacency - meaning it operates with Iran's tacit approval, if not direct direction.
The choice of Stryker is deliberate in its messaging. Medical device companies sit at the intersection of civilian life and military supply chains - they provide the equipment used in military hospitals treating wounded US soldiers returning from the Gulf theater. Breaching Stryker signals that Iran views the entire American industrial base as a legitimate target, not just defense contractors.
The Target Map: What Iran's Hackers Are Actually Hitting
Stryker is the most prominent confirmed US victim, but it represents one data point in a much wider pattern of Iranian cyber operations that began the moment the first missiles flew on February 28.
According to cybersecurity researchers and intelligence compiled by SITE Intelligence Group, pro-Iranian hackers have in the first 13 days of the war successfully:
Confirmed Iranian Cyber Operations - Days 1-13
- Penetrated surveillance camera networks across the Middle East to improve Iran's missile targeting against US and Israeli positions AP
- Breached data centers across the Gulf region, disrupting logistics for US military contractors AP
- Compromised industrial control systems at facilities in Israel AP
- Attacked a school network in Saudi Arabia and airport systems in Kuwait AP
- Breached Stryker Corporation's global Microsoft network (US, Day 13) AP, SEC
- Attacked a nuclear research facility in Poland, under investigation for Iranian attribution AP
The camera hacking operation is particularly significant. It is not vandalism - it is battlefield intelligence gathering. By accessing real-time surveillance feeds across the region, Iranian operators can monitor US troop movements, identify targeting windows, and feed live data to missile crews. This is cyber warfare as active force multiplier. AP
The Polish nuclear facility attack, if confirmed as Iranian, would represent a major escalation into European critical infrastructure. Polish authorities acknowledge they are investigating but note that attribution is still being determined, and that another actor could be exploiting the war to mask its identity. But analysts note that timing - the attack came shortly after Poland announced additional military support packages for Israel - is not a coincidence.
Meanwhile, on Telegram channels monitored by SITE Intelligence Group, pro-Iranian hackers openly discussed their strategic ambitions in language that leaves little doubt about intent.
"The datacenters need to be taken out. They host the brains of USA's military communication and targeting systems."
- Unidentified user in pro-Iranian hacker Telegram channel, as reported by SITE Intelligence Group
How Iran Built This Cyber Arsenal - And Why It Was Ready
Iran's cyber capabilities did not emerge overnight. The country has spent the better part of a decade constructing offensive hacking infrastructure, and the war has simply activated what was already prepositioned inside American networks.
The record is not abstract. In the years before February 2026, Iran-linked hackers successfully infiltrated the email systems of Donald Trump's 2024 presidential campaign, an operation that US intelligence attributed to the Islamic Revolutionary Guard Corps. AP They targeted American water treatment plants in a campaign that prompted an emergency warning from the Environmental Protection Agency. AP They repeatedly probed the networks of US defense contractors and military supply chain companies.
Iran cultivated these capabilities with a specific strategic purpose: they serve as the asymmetric equalizer against a conventional military opponent it cannot match in open battle. The United States has carrier groups, stealth bombers, and precision-guided munitions. Iran has missiles, proxies, the Strait of Hormuz, and a cyber army that has spent years burying itself inside the infrastructure that runs American daily life.
Kevin Mandia, founder of Mandiant and one of the most experienced voices in American cybersecurity, summarized the current moment in terms that stripped away any remaining ambiguity.
"Something is going to happen because the gloves are off."
- Kevin Mandia, Founder, Mandiant and Armadin
The phrase "gloves are off" has a specific meaning in this context. During peacetime, state-sponsored hackers typically operate under rules of engagement that limit the damage they cause to avoid triggering kinetic retaliation. They prefer espionage and exfiltration over destruction. When those constraints are removed - as they are in active armed conflict - the same operators who were previously restrained by geopolitical calculation are now free to maximize disruption.
Iran is in a war in which it is absorbing daily airstrikes on its territory and watching its military infrastructure reduced piece by piece. The political and strategic calculus that previously kept its cyber operations in espionage mode has dissolved. The only question now is which American target will be next, and how destructive the operation will be.
America's Weakened Defenses: Staff Cuts, DHS Shutdown, and the Civilian Gap
The timing of Iran's cyber offensive coincides with an extended period of deliberate weakening of American cybersecurity infrastructure, driven by budget cuts and a federal shutdown that has left the Department of Homeland Security operating without appropriated funds for nearly four weeks.
The DHS shutdown began February 14 and remains unresolved. Senate Democrats and Republicans remain deadlocked over immigration policy attached to the funding bill, while TSA lines at airports around the country grow longer and critical departmental operations limp forward on emergency authority. The Cybersecurity and Infrastructure Security Agency - CISA, the federal body whose explicit mandate is to protect American critical infrastructure from exactly this kind of attack - is operating in degraded mode. AP
The cuts did not begin with the shutdown. According to Democratic senators who wrote to Defense Secretary Pete Hegseth this week demanding accountability for the school strike, the Trump administration has systematically reduced personnel and budget at units across the national security apparatus responsible for protecting civilian life. Those cuts extended to US Central Command's civilian casualty prevention office - the same body whose underfunding likely contributed to the Minab school disaster. AP
The Civilian Protection Center of Excellence - a congressionally mandated Pentagon office signed into law in 2022 to reduce civilian casualties in US strikes - has been gutted under the current administration, with budget and personnel cuts eliminating much of its capacity. AP The same logic that stripped military strike oversight of its civilian protection layer has been applied to cybersecurity: prioritize speed and lethality, reduce oversight and protection infrastructure.
The practical consequence is visible in how American cybersecurity professionals describe the threat environment. Local water plants and healthcare facilities - the "soft underbelly" of American critical infrastructure that analysts consistently identify as the most vulnerable - lack the resources, expertise, and software patching cycles to withstand sustained attacks from well-resourced state-adjacent groups. These were never hardened targets. They were always the path of least resistance for any adversary willing to cause pain to American civilians. AP
US Cybersecurity Capacity Under Pressure
- DHS shutdown in week 4 - CISA operating under emergency authority with reduced staffing
- Trump administration cut Civilian Protection Center of Excellence at Pentagon
- CENTCOM civilian protection resources reduced prior to war
- Local water plants and hospitals remain chronically underfunded for cybersecurity
- DHS appropriations bill the only unfunded bill remaining in FY2026 budget cycle
- Senate deadlocked: Democrats blocking ICE funding, Republicans refusing to accept oversight changes
Iran's Cyber Timeline: Thirteen Days of Digital Warfare
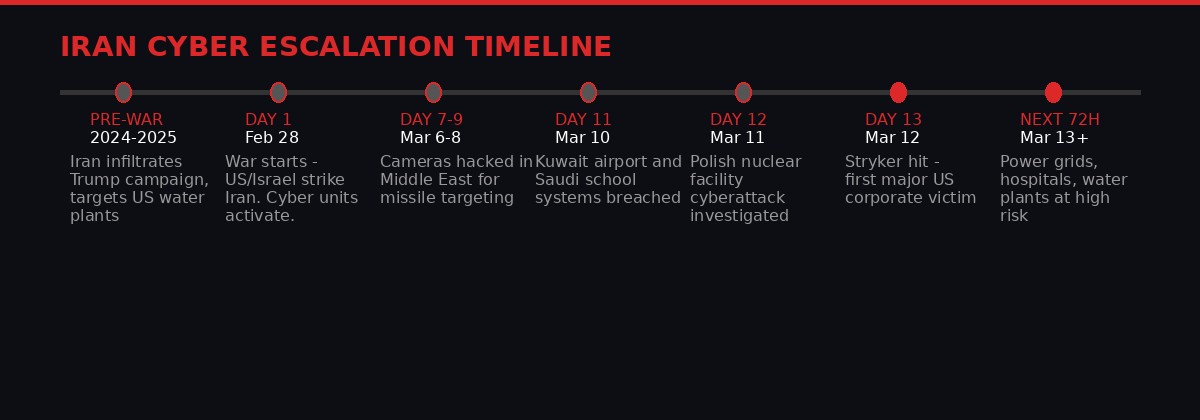
Iran's documented cyber operations from prewar positioning through Day 13. Graphic: BLACKWIRE
Understanding the pace of Iran's cyber escalation requires seeing the operations in sequence. What began as background espionage and pre-positioning has accelerated, week by week, toward direct attacks on American corporate targets.
The Escalation Path: What Intelligence Analysts Say Comes Next
Cybersecurity professionals are largely unified in their assessment of where Iranian operations will point next - and the answer is uncomfortable. The Stryker attack was chosen for its ripple effects: a medical supply company hitting news cycles serves the propaganda goal of demonstrating that the war has real costs for ordinary Americans. But the strategic prize targets are harder, and their disruption would cause genuinely consequential harm to American life.
US defense contractors and government vendors sit at the top of the threat list. Companies that build weapons systems, manage military logistics, maintain satellite communications, or provide IT infrastructure to federal agencies have been identified by researchers as high-probability targets. If Iran's hackers can disrupt the supply chains feeding the military campaign against it, that is a meaningful strategic win - it extends the timeline of the war, increases costs, and potentially forces operational changes in the field. AP
Critical infrastructure presents a different type of risk. Power stations, water treatment plants, hospitals, and railways are not primarily military targets - they are civilian. But Iranian strategy has shown a consistent willingness to cause civilian pain as a form of political pressure. The theory is straightforward: if American citizens start experiencing power outages, water system disruptions, and hospital system crashes, the domestic political cost of the war rises and pressure mounts on Washington to negotiate or de-escalate. AP
The Telegram communications monitored by SITE Intelligence Group suggest Iran's hackers are specifically targeting data centers because they "host the brains of USA's military communication and targeting systems." This is partly true - many US military communications do route through commercial cloud infrastructure - but it is also imprecise in a way that makes civilian collateral damage more likely, not less. Hitting Amazon Web Services in the UAE, for instance, disrupts both military systems and the civilian internet infrastructure of an entire region. AP, SITE Intelligence Group
The more immediate risk for most Americans is healthcare. Hospital systems that lack the funding for cybersecurity professionals, that run legacy software on unpatched machines, that depend on internet-connected medical devices - these are the soft underbelly that pro-Iranian hackers have already identified and discussed. A successful attack on a major hospital network during wartime would be catastrophic: patient records lost, surgical scheduling disrupted, monitoring equipment potentially compromised, ambulances diverted. This is the scenario that keeps American cybersecurity officials awake at night.
Mojtaba Khamenei's First Statement - And What the Cyber War Means
The cyber escalation takes on added urgency given Iran's supreme leader's first public statements since assuming power following the death of his father and wife in the war's opening hours.
In a statement read by a state television anchor on March 12 - Khamenei himself has not appeared on camera since being wounded in the February 28 strike - Iran's new supreme leader promised to keep fighting, vowed "more pain" for Gulf Arab states, and threatened to open "other fronts." He said he was keeping a "file of revenge." AP
That phrase - "other fronts" - is significant. Iran's kinetic options are constrained by the overwhelming conventional military superiority of the US-Israeli coalition and by the economic damage of sustained airstrikes on its infrastructure. Cyber warfare is precisely the kind of "other front" that Khamenei's statement telegraphs: low cost to Iran, high cost to the United States, deniable, and not subject to the same rules of engagement that govern kinetic retaliation.
Netanyahu, speaking at a news conference the same day, dismissed Khamenei as a "puppet of the Revolutionary Guards" and said Israeli strikes were "creating the optimal conditions for the fall of the regime." The exchange illustrates how each side reads the conflict: Israel sees regime change as achievable through military pressure; Iran sees attrition - economic, cyber, and through proxy operations - as its path to making the war too costly to continue. AP
Both readings may be correct simultaneously, and that is precisely what makes the next phase of the conflict so dangerous. If Iran believes it is fighting for regime survival, the cyber operations it is willing to authorize have no upper bound.
What Businesses and Infrastructure Operators Need to Know Now
The threat intelligence community is consistent in its advice, though that advice requires resources that many potential targets do not have. The practical guidance for businesses and infrastructure operators operating in an elevated threat environment centers on a few core principles.
Patch immediately. Iran's hackers consistently exploit known vulnerabilities that vendors have already issued patches for - the gap between patch release and deployment is the attack window. Organizations that maintain rigorous patching cycles are significantly harder targets than those that do not. This is especially true for Microsoft systems, which Stryker's breach confirms remain a primary avenue of attack. AP, Recorded Future
Segment networks. Many successful attacks - including those that take down operational technology like industrial control systems or hospital monitoring equipment - succeed because flat network architectures allow attackers to move laterally from an initial breach point to high-value targets. Segmentation limits blast radius.
Assume breach. The most dangerous assumption any organization can make right now is that because it has not been attacked, it has not been compromised. Iran prepositioned access inside American networks years before the war began. Organizations in defense, healthcare, energy, and water should assume that persistent access may already exist and should be conducting threat hunts accordingly.
Report to CISA. Despite the DHS shutdown degrading its capacity, CISA remains the primary federal point of contact for critical infrastructure operators facing active threats. Intelligence sharing is reciprocal - information organizations share about attack methods helps build the picture that protects other potential targets.
Immediate Action Guidance (CISA)
- Patch all internet-facing systems immediately - prioritize Microsoft products
- Enable multi-factor authentication on all accounts without exception
- Segment operational technology (OT) from information technology (IT) networks
- Conduct threat hunting for persistence mechanisms - assume prior compromise
- Review and test offline backup procedures for critical systems
- Report anomalous activity to CISA: report.cisa.gov
- Defense contractors: review physical security of server rooms alongside cyber posture
The core message from cybersecurity professionals is that the Stryker attack is not an aberration and not a ceiling. It is an opening shot in a cyber campaign that Handala and other pro-Iranian groups have signaled they intend to expand. The war has given them motivation they did not have before, and 13 days of combat have removed whatever restraint existed before February 28.
Kevin Mandia's assessment that "something is going to happen" is not a prediction. It is a reading of indicators that, in his experience, have never been wrong.
The question is not whether the next major attack on American infrastructure comes. The question is which hospital goes dark first, which water plant loses control of its chemical dosing systems, which power substation drops offline in a grid that was already strained by a cold spring. That answer will come from whichever organization made the mistake of thinking that a war in the Middle East was someone else's problem.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram