The Fraud Factory: Inside the $1 Billion Investment Scam Machine
A German court is prosecuting the men who built the software that powered a global investment fraud empire spanning eight countries. For the first time, the architects - not just the foot soldiers - face justice. The scale of what they built is staggering.
The fraud factory's supply chain ran from affiliate marketers to shell companies, processing billions in stolen money. | BLACKWIRE / PIL graphic
The first clue is always the software. Behind every fake trading platform - every "Huludox," every "Nobeltrade," every "Forbslab" that appeared in the inbox of a retiree in Barcelona or a nurse in Stockholm - there was code. Elegant, well-maintained, purpose-built code. And behind that code, there were people who wrote it, sold it, updated it, and got paid a percentage of everything it stole.
This is the central finding of a landmark series of trials now underway at Bavaria's Bamberg Regional Court: the enablers of industrial-scale investment fraud are finally being prosecuted alongside the people who committed it.
In March 2026, a German court opened proceedings against a man identified as "Shay B.," the CEO of an Israeli software company called Airsoft. Before him, in February, Mikheil Biniashvili - an Israeli-Georgian national who built and sold a competing scam software platform called Puma TS - was sentenced to seven years and six months in prison. Together, these two men supplied the technological backbone for what OCCRP has documented as a fraud operation that drained at least $250 million from victims across Europe and beyond. [OCCRP, March 2026]
Investigators now believe the true scale is much larger. And the trials are forcing courts to answer a question with implications for the entire technology industry: when does providing software to criminals make you one of them?
KEY FACTS AT A GLANCE
- Airsoft CEO "Shay B." on trial for 4 counts of commercial and organized fraud
- Airsoft software deployed across Huludox, Fibonetix, Nobeltrade, Tradecapital, Forbslab
- Puma TS software deployed by 397 different scam brand platforms
- Biniashvili sentenced to 7.5 years - admitted victims lost approx. $150 million
- Milton Group network operated call centers in Ukraine, Albania, Georgia, and elsewhere
- Victims received up to 500 cold calls per day per center per agent
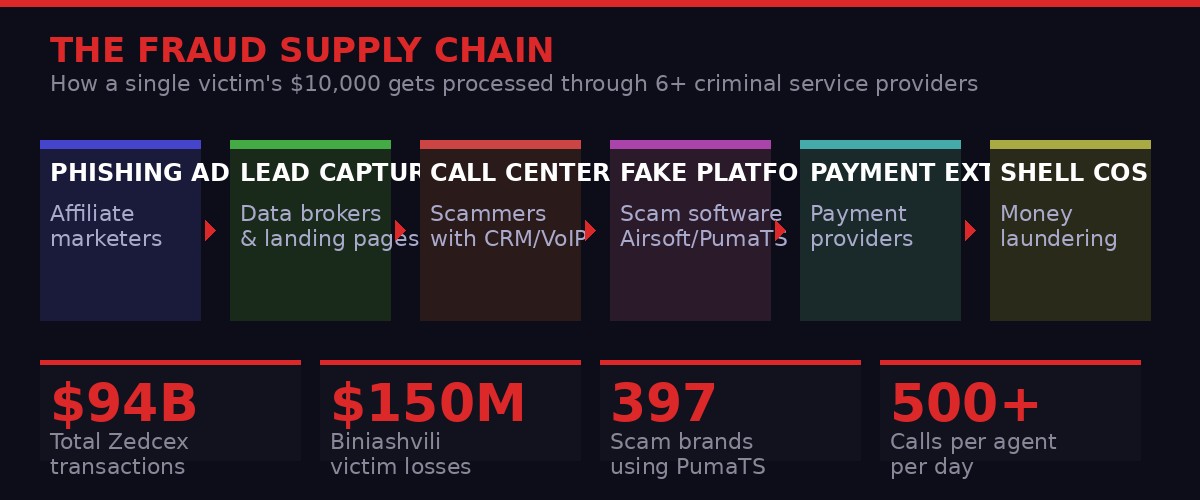
The industrial fraud supply chain: how money moved from victim to criminal, passing through six or more service providers at each stage. | BLACKWIRE / PIL graphic
The Architecture of Industrial Fraud
The modern investment scam is not a lone criminal making phone calls from a back room. It is a corporation, complete with HR departments, software subscriptions, offshore payroll systems, and quarterly performance reviews. What OCCRP's "Fraud Factory" and "Scam Empire" investigations revealed over several years is that these operations were structured with the same cold logic as any legitimate business - except that the product was theft.
At the heart of every call center was CRM software - customer relationship management tools, the same category of software used by every legitimate sales company in the world. The difference was what these systems tracked: not real clients with real investments, but victims. Their financial history. Their emotional vulnerabilities. How much money they had left. What lies had already been told to them. What pressure remained to be applied.
The scam worked in stages. First, affiliate marketers would run phishing advertisements on social media, often using fabricated celebrity endorsements - fake quotes from local newsreaders, politicians, footballers - to convince marks that a legitimate investment opportunity existed. Victims who clicked would be taken to professional-looking landing pages and asked to enter their phone numbers and email addresses. These "leads" were then sold to call centers in bulk. [OCCRP, Scam Empire Investigation]
Once the data reached the call center, agents - typically young, multilingual, paid on commission - would begin making contact. The platforms they pointed victims toward were not real exchanges. They were simulations, controlled entirely by the scammers. Agents could manipulate the "portfolio value" shown to the victim in real time, manufacturing apparent gains to encourage further deposits. Then, when the victim tried to withdraw, demands for tax payments, verification fees, and compliance charges would drain whatever remained.
"I get people on the phone and show them a video showing various people earning millions of euros by joining a Bitcoin stock exchange, and I tell them it is a good chance for them to earn. I know we cheat people." - A call center insider, speaking to OCCRP under anonymity conditions
This was the machine. What made Airsoft and Puma TS special was that they turned every piece of it into a product that could be sold as a subscription service. Software-as-a-Service - for fraud.
Shay B. and Airsoft: The Second Trial
On March 2, 2026, opening arguments began in the Bamberg Regional Court against a man identified only as "Shay B.," the Israeli CEO of a company called Airsoft. He faces four counts of commercial and organized fraud, covering a period from March 2015 to at least the end of June 2021 - more than six years of alleged criminal enablement.
The indictment, obtained by OCCRP, describes Airsoft as providing a "brokerage all-in-one solution" - software that provided scam operators with everything they needed to simulate a trading platform and deceive investors. Prosecutors allege Shay B. "knowingly and willingly" supplied this tool to criminal groups, taking a cut of the revenue generated from each scam it powered.
The Bamberg Public Prosecutor's Office took the unusual step of opening the trial by having prosecutors spend nearly two hours reading the names and losses of individual victims. Their combined losses totaled more than 94 million euros - roughly $108 million. It was a theatrical but deliberate choice: to force the court, and the defendant, to confront the human scale of what the software enabled. [OCCRP, March 2026]
Airsoft's software was deployed across at least five named platforms: Huludox, Fibonetix, Nobeltrade, Tradecapital, and Forbslab. The operators of those platforms were convicted by the same Bamberg court in 2025 for operating scams run from call centers in Bulgaria, Serbia, Ukraine, Georgia, Israel, and Kosovo. Now prosecutors are working up the supply chain.
Shay B.'s defense team has not denied the facts entirely - a press officer at the court confirmed he has "partially admitted" the facts of the case. But his lawyers are challenging the legal threshold for criminal liability, arguing that the case raises fundamental questions about when a software provider becomes legally responsible for how their product is used. In a written statement, they said: "The central question before the court is at what point, and under what legal conditions, a software provider may be held criminally liable for the misuse of its product by third parties."
Prosecutors are not buying the innocent-vendor defense. The indictment states explicitly that Airsoft went beyond simply providing software: "In some cases - depending on the respective authorizations - the involvement of Airsoft employees was required, which did indeed occur." The allegation is not that Airsoft built a neutral tool that bad actors misused. The allegation is that Airsoft personnel actively participated in the fraud operations. Proceedings are expected to conclude this month.
Mikheil Biniashvili and Puma TS: The First Conviction
If Shay B.'s trial is the second act, Mikheil Biniashvili's conviction in February 2026 was the moment the strategy of prosecuting software vendors was validated. Biniashvili, an Israeli-Georgian citizen who spent years building and operating call-center fraud infrastructure, accepted a plea deal and was sentenced to seven years and six months in prison.
His Puma Trading System - known as Puma TS - was described by prosecutors as an "all-in-one service" for simulating non-existent trading activity on fraudulent platforms. The numbers are staggering: Puma TS was deployed by 397 different "scam brand" platforms. Not 397 victims, not 397 calls - 397 entirely separate fake trading brands, each with its own website, its own fabricated executives, its own team of agents calling victims across different countries. [OCCRP, 2026]
Like Shay B., Biniashvili was also connected directly to the Milton Group - the fraud network whose internal documents, a whistleblower party recording, and New Year's party photographs became the foundation of OCCRP's multi-year Fraud Factory investigation. Biniashvili was previously a member of the Milton Group's call-center network, then graduated to selling software to the industry. He was fully aware his clients were running scams, and he took a percentage of their illicit profits directly.
The total losses attributable to Biniashvili's activities were estimated at approximately $150 million. His prison sentence, though substantial, has been noted by anti-fraud advocates as a meaningful signal: enabling industrial fraud infrastructure now carries serious personal consequences, even for those who stayed several degrees removed from the actual fraud calls.
That assessment comes from Yaniv Hanoch, a professor of decision science at the University of Wolverhampton who studies the cyberscam sector. He was commenting specifically on the Bamberg trials and the novel strategy of prosecuting alleged enablers. The logic is straightforward: the actual scam callers are often young, replaceable, and spread across jurisdictions with limited legal cooperation. The software vendors are fewer in number, their contributions are more distinctive, and the profit trail is cleaner.

Timeline of key events in the Fraud Factory investigation, from the first OCCRP exposé through the 2026 Bamberg software vendor trials. | BLACKWIRE / PIL graphic
The Milton Group: How It Started
The Bamberg trials are the culmination of an investigation that OCCRP began years earlier, when a whistleblower smuggled internal documents and secret recordings out of a boiler-room operation in Kyiv. The Milton Group was running its fraud operation out of a shopping mall. Young agents, mostly Ukrainian, worked in open-plan offices calling victims across Europe, pushing them toward fake investment platforms with names like Capital Bear, WinTrade, and BTCClicks.
What first appeared to be a local Ukrainian scam operation turned out to be an international franchise. The New Year's party in January 2020 - captured by the same whistleblower who attended as an informant - was OCCRP's first window into the network's true scope. An Albanian defense ministry adviser, identified by OCCRP as Amant Josifi, was photographed in the VIP section alongside Milton Group CEO Jacob Keselman. At another party in Tbilisi, Keselman was photographed with figures connected to a Georgian call-center operation. [OCCRP, Fraud Factory Investigation]
The Albanian connection was particularly striking. Josifi's call center, run through two companies - CTA Groupe Shpk and APA Liaison Shpk - was operating in Tirana while he simultaneously held a government advisory position. His mother was a former judge turned senior civil service official. His former business partner was a brother of Prime Minister Edi Rama. The fraud operation had roots inside the Albanian state's social networks, however loosely.
Josifi denied formal ties to Milton and said his center was unrelated to their operations. But the insider who spoke to OCCRP described a center structured identically to the Kyiv operation: hundreds of agents making up to 500 calls a day to targets across Europe, in multiple languages, selling fake investment brands including CryptoKartal, AurumPro, and Virtual Stocks.
The Georgian Dimension
Another node in the network stretched to Tbilisi. The same party photographs that revealed the Albania connection also showed a man identified as "Danilo Z" in regular company with Keselman and other Milton Group figures. He was photographed at New Year's celebrations in both Tbilisi and Tirana, tracking the network's geography through Instagram metadata.
Biniashvili himself was based in Georgia before his arrest. His operation there - which ran under the name "Morgan Limited," visible in party backdrop photos - contributed directly to the network documented in OCCRP's investigation. What prosecutors were eventually able to prove was that Biniashvili was not a passive software vendor but an active participant: he ran call-center operations himself, sold his software to others, and took commissions from the proceeds. The distinction between vendor and perpetrator collapsed entirely.
The Ecosystem: Thirty Companies, One Machine
One of the most revealing components of the OCCRP investigation was not the exposure of individual fraudsters but the mapping of the entire service ecosystem they depended on. In their Scam Empire investigation, journalists documented dozens of companies across the full fraud supply chain - from data collection to money extraction. [OCCRP, Behind the Scam, 2024]
The chain begins with affiliate marketers - companies like MGA Team, CRYP, Sierra Media, and Oray Ads - who harvest victim data through phishing ads placed on social media platforms. These ads frequently violate platform policies but pass through automated moderation. Meta, Google, and Taboola all collected advertising revenue from ads promoting investment scams, according to OCCRP's analysis.
Once a victim had been identified and contacted, the scam infrastructure required VoIP phone services to make the volume of calls required. Companies like Coperato and Squaretalk provided the telephony layer - critically, their services allowed agents to display any country code they chose, making calls appear to originate from London, Zurich, or New York when they were actually coming from a call center in Bulgaria or Kosovo.
The money extraction layer was equally sophisticated. Services like Bankio/Anywires and Britain Local operated as shadow payment processors, funneling victim deposits through accounts belonging to shell companies before routing the funds to their final destination. Internal documents showed these intermediary services charged 10 to 17 percent fees - far above any legitimate payment processor - reflecting the risk premium for facilitating financial crime. The scammers also coached victims on how to answer questions from their own banks to prevent their transfers from being flagged as suspicious.
Shell companies completed the circuit. Companies like Selterico SL, Greencode Connection Limited, Purplesun Limited, and Intek Systems Limited appeared in the leaked documents as entities used to receive and launder money, as well as to pay the call centers' operating costs - creating a corporate veil between the criminal operation and any individual who might be traced. Most were registered in jurisdictions with minimal beneficial ownership transparency requirements.
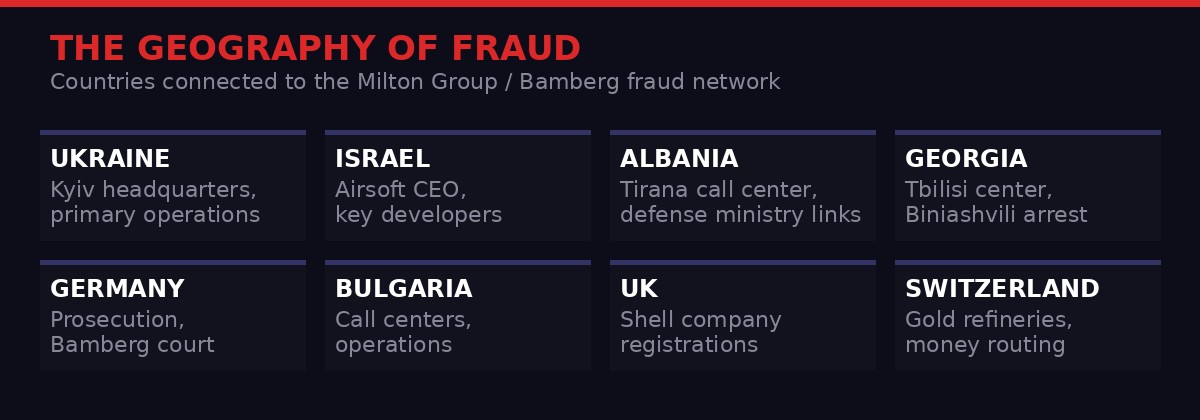
The fraud network's geographic footprint spanned from Ukraine and Georgia to Albania, Israel, Germany, and beyond. | BLACKWIRE / PIL graphic
The Legal Question the Trials Must Answer
Shay B.'s defense team has framed their client's case as a test of where criminal liability ends for software vendors. The argument is familiar: a knife manufacturer is not responsible when their knife is used in a stabbing. A phone company is not responsible when their network carries criminal calls. At what point does the software vendor become criminally liable?
The Bamberg prosecutors have an answer: when you knew what your software was being used for, took a percentage of the criminal proceeds, and had your own staff directly assist in fraud operations. That is not the knife manufacturer. That is the accomplice who handed the knife to the attacker and asked for 15 percent of the robbery proceeds.
The indictment against Shay B. explicitly alleges that the scam operators could not have functioned without Airsoft's active involvement. The software did not just exist - it was configured, maintained, and operated with Airsoft's knowledge and participation. Prosecutors say the CEO was aware throughout.
"It is a great idea to go after the alleged enablers. Since it is difficult to catch the actual scammers, disrupting the process is an excellent idea and sends a message to others." - Yaniv Hanoch, Professor of Decision Science, University of Wolverhampton
The legal principle at stake - criminal liability for platform providers who knowingly enable crime - has implications beyond investment fraud. It touches the edge of questions being debated in every major jurisdiction about technology companies, social media platforms, and the limits of the "neutral tool" defense. Bamberg is not Silicon Valley, and Airsoft is not Google. But the legal precedent being established in a Bavarian regional court in spring 2026 will resonate well beyond Germany's borders.
Graham Barrow, a British anti-money-laundering expert consulted by OCCRP, has for years documented how the UK's Companies House registry was weaponized by criminals to create fake corporate directors. The Elizabeth Newman case - in which a fictitious "CEO" of two Iranian crypto exchanges was represented by stock footage - is merely the most vivid example of a systemic problem. In the fraud call center world, the same principle applied: fake companies, fake directors, fake platforms, real money stolen from real people.
What Happens Next: The Road to Justice Is Long and Incomplete
The Bamberg trials represent a meaningful escalation in the prosecution of industrial fraud. But they are also a reminder of how much remains beyond reach. The ring leaders convicted in 2025 - the operators of Huludox, Fibonetix, Nobeltrade, Tradecapital, and Forbslab - were only caught after years of investigation. Biniashvili cut a plea deal. Shay B.'s verdict is expected later this month. The affiliate marketers, the VoIP providers, the shell company formation agents - most remain unprosecuted.
Jacob Keselman, the former Milton Group CEO photographed at New Year's parties in Kyiv, Tirana, and Tbilisi, had not been publicly charged as of this writing. The Albanian defense ministry adviser photographed alongside the network's principals continued in his role after OCCRP's initial reporting. The full political network that sheltered these operations from local law enforcement scrutiny - in Ukraine, Albania, Georgia, and elsewhere - has never been subjected to serious accountability.
The structural problem is geography. Investment fraud operations are deliberately spread across jurisdictions with minimal legal cooperation. The victim is in Spain. The call center is in Bulgaria. The software company is in Israel. The shell companies are in the UK and Cyprus. The money ends up in Georgia or the UAE. No single law enforcement authority has jurisdiction over all of it, and obtaining mutual legal assistance treaties across all these jurisdictions takes years. Fraudsters depend on this friction - it is a feature of the business model, not a bug.
European authorities have recently pushed for tighter anti-fraud coordination. Germany's Central Office for Cybercrime, based in Bamberg, has emerged as one of the most aggressive prosecutors of online financial fraud in the continent. Their approach - working methodically up the supply chain from foot soldiers to enablers - is the most viable strategy available within existing legal frameworks. Each conviction at the Airsoft and Puma TS level makes the next prosecution easier: it establishes that software vendor liability is real, that taking a percentage of fraud proceeds makes you a participant, and that "I just built the tool" is not a defense.
For the hundreds of thousands of people who lost savings, retirement funds, and life's work to these platforms, the trials are significant but incomplete. Victim recovery in investment fraud cases is notoriously poor: by the time a case reaches trial, the money has typically been layered through so many shell companies and jurisdictions that meaningful recovery is impossible. Prosecutors at Bamberg read the victims' names for two hours. Most of them will never be made whole.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram