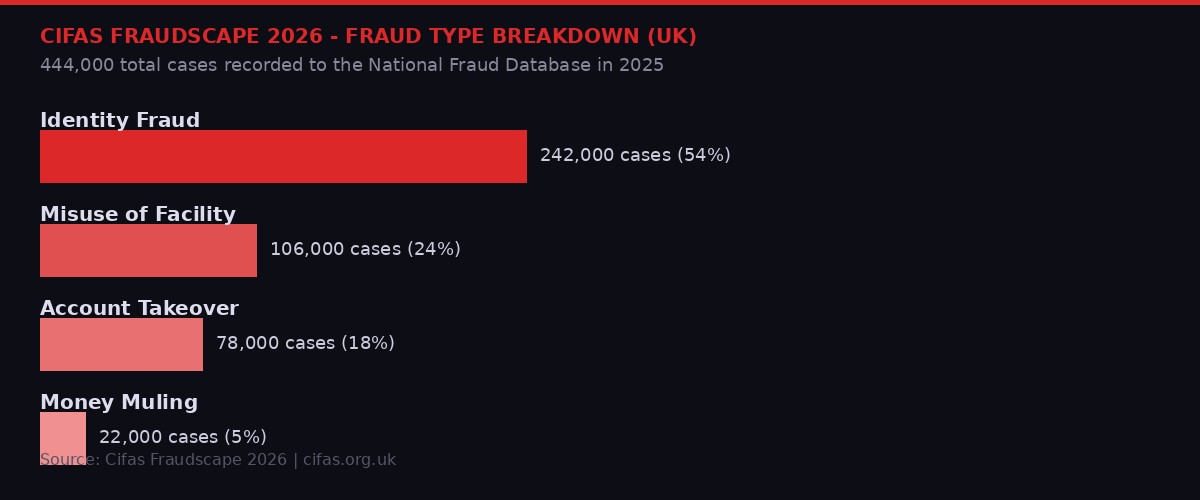
Cifas Fraudscape 2026: Identity fraud dominates with 242,000 cases, accounting for 54% of all fraud filings in the UK in 2025. Source: Cifas.
The number alone should stop you cold. In 2025, fraud prevention service Cifas recorded 444,000 cases filed to the UK's National Fraud Database - the highest total in the database's history, and a 6% increase on the already-record year before it. That works out to more than 1,200 cases per day. Every 72 seconds, someone in Britain had their identity stolen, their account hijacked, or their savings stolen by a network they never saw.
But the raw number misses the more disturbing story. The real headline is the architecture behind it - the industrialization of fraud into what Cifas CEO Mike Haley calls a system that "mimics the size and structure of large corporations." Criminal networks are no longer opportunistic. They have been rebuilt from the ground up using the same tools that power Silicon Valley: AI, cloud infrastructure, data pipelines, and synthetic identity generation. They have call center managers and shift rotations and KPIs measured in euros stolen per hour.
The week of March 11-17, 2026 crystallized just how acute this threat has become. Cifas published its annual Fraudscape report on March 12. Meta announced it had removed 10.9 million scam-linked accounts on March 11, alongside a new joint operation with the FBI and Royal Thai Police that led to 21 arrests. On March 13, Eurojust announced the takedown of a criminal proxy network that had silently infected 369,000 modems across 163 countries. And on March 16, at a UN Global Fraud Summit in Vienna, eleven major technology companies - including Google, Microsoft, Amazon, LinkedIn, and OpenAI - signed the Industry Accord Against Online Scams and Fraud.
All of it points to the same conclusion: fraud is no longer a crime. It is an industry. And right now, it is winning.
The Fraudscape: A Record That Should Not Exist
Cifas is a not-for-profit fraud prevention service with nearly 800 member organizations drawn from banking, insurance, retail, and telecommunications across the United Kingdom. Its National Fraud Database is the single most comprehensive real-time picture of fraud activity in the country. When Cifas says 444,000 cases is a record, it is a record built on top of a previous record, which was built on top of another record. UK fraud has now climbed for five consecutive years.
The Fraudscape 2026 report, published March 12, lays out what that looks like sector by sector. Identity fraud - where criminals use stolen or synthesized personal information to open accounts, take out credit, or impersonate individuals - remains the dominant category at 242,000 cases, representing 54% of all filings. That figure actually fell 3% compared to 2024, but Cifas analysts are careful to note this does not represent progress. It represents a tactical shift. Criminals are migrating away from straightforward identity fraud - which detection systems have learned to flag - toward account takeover, a more patient and harder-to-detect method.
Facility takeover - hijacking existing accounts rather than opening new ones - rose 6% to more than 78,000 cases. Account takeover in the telecommunications sector alone now constitutes 62% of all such cases, up from 48% the year before. The mechanism is SIM swapping: criminals use stolen personal data to convince mobile carriers to issue replacement SIM cards, effectively transferring a victim's phone number to a device the criminal controls. From there, two-factor authentication becomes worthless. Every account tied to that phone number is accessible. Unauthorized SIM swaps rose 38% in 2025 compared to 2024, per the Cifas data.
Perhaps the most alarming single figure in the report is misuse of facility - where accounts are opened legitimately and then exploited, often through recruited "money mules" who allow their accounts to receive and forward criminal proceeds. This category surged 43% in 2025. Newly introduced money mule filings alone added 22,000 cases. Payment fraud within this category rose 239% compared to 2024 and now accounts for 40% of all misuse filings.
"Our data and intelligence show how fraud is being industrialised, with AI accelerating crime that is increasingly digital, organised and international. Fraud must be treated as a national enforcement priority." - Mike Haley, CEO, Cifas, March 12, 2026
Nick Sharp, Deputy Director of Fraud at the UK National Crime Agency, offered a figure that contextualizes the scale: fraud now accounts for 45% of all crime in England and Wales. Not 45% of financial crime. Not 45% of cybercrime. 45% of all crime - everything from burglary to assault to drug trafficking combined. The NCA has classified fraud as a National Security and Serious Organised Crime risk, the highest operational designation available.
The Factories: Where the Fraud is Made
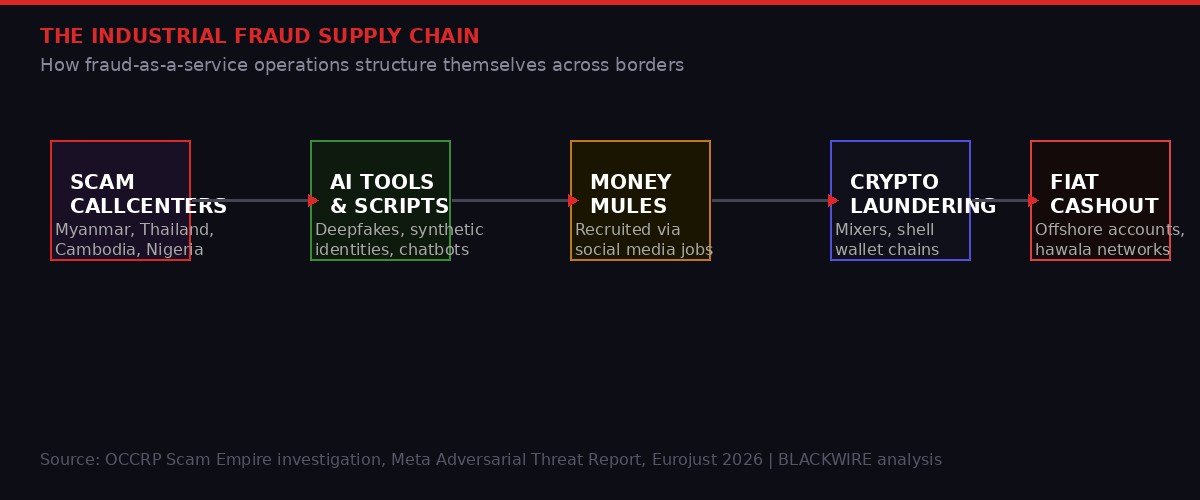
The industrial fraud supply chain: from scam call centers in Southeast Asia and West Africa through AI tools, money mules, and cryptocurrency laundering to final fiat cashout. BLACKWIRE analysis.
In March 2025, OCCRP published what it called Scam Empire - an investigation built on an unprecedented leak of nearly two terabytes of internal data from two major scam operations. The material included thousands of hours of recorded phone calls, screen recordings of agents working their victims, internal spreadsheets tracking revenue targets, and training documents that read like onboarding manuals at legitimate corporations.
What the investigation revealed was not the image of a lone fraudster working from a basement. It was something closer to a call center franchise model - industrial in structure, metrics-driven in management, and deliberately insulated from the jurisdictions that might prosecute it. Analysts who worked the scams had daily quotas measured in euros extracted from victims, who were referred to internally by nationalities: "the German," "the Swedish widow," "the retired American."
The geographic footprint of these operations has become well-documented. Myanmar's Myawaddy region - controlled by ethnic armed militias operating in ungoverned border zones - hosts some of the largest scam compounds in Southeast Asia. Similar facilities operate in Cambodia, Laos, and parts of Thailand. Meta's enforcement team, which has been running what it calls "Joint Disruption Weeks" alongside the FBI and Royal Thai Police, announced on March 11, 2026 that a second coordinated operation had disabled over 150,000 accounts associated with scam center networks, contributing to 21 arrests by Thai police.
But Southeast Asia is only one node. Meta's announcement also referenced a February 2026 operation in which the Nigerian Police Force, the UK National Crime Agency, and Meta investigators jointly dismantled a scam center in Agbor, Delta State, Nigeria. Seven suspects were arrested. The center had been running fake cryptocurrency trader profiles on Facebook and Instagram, targeting British and American citizens.
The Nigerian arrest connects to a pattern Cifas and the NCA have both flagged: scam operations are deliberately cross-jurisdictional. The fraud is planned in one country, executed through technical infrastructure in another, and the money is moved through a third and fourth. By the time any single law enforcement agency has the legal authority to act, the money has moved three times and the operators have changed phones.
The Scammer's Recruitment Problem - and How They Solved It
Money mules represent one of the most cynical innovations in the modern fraud supply chain. These are individuals - often unwitting, occasionally complicit - whose legitimate bank accounts are used to receive and forward criminal proceeds, creating a layer of apparent legitimacy between the fraud and the final cashout.
Cifas data reveals how this recruitment has evolved. In 2025, 35% of Gen-Z respondents surveyed by Cifas said they would transfer money for a stranger in exchange for a fee. A fifth of respondents did not believe money muling was illegal. Criminal networks have seized on this, engineering elaborate recruitment campaigns that run on social media: fake job postings promising quick cash for "payment processors," "financial assistants," or "administrative support" roles. The work consists of receiving wire transfers and moving them onward. Participants are told it is arbitrage, import-export float, or a sign-on bonus waiting period. By the time they discover they are moving criminal proceeds, their account has been flagged and they face potential prosecution alongside the people who recruited them.
The fastest-growing mule age demographic, per Cifas, is under 16 years old.
The AI Upgrade: How Machine Learning Broke Identity Verification
For most of the past decade, the primary defense against identity fraud was the same: require the person opening the account to confirm they are who they say they are. Present a document. Take a photograph. Submit to a biometric check. These systems worked reasonably well against humans operating at human scale.
They are increasingly ineffective against AI.
Cifas Director of Intelligence Stephen Dalton spelled out the threat in the Fraudscape 2026 report: "The use of synthetic identities is becoming industrialised, with criminals building convincing long-term profiles that blur the lines between real users and AI-generated imposters." A synthetic identity is not a stolen identity. It is a constructed one - assembled from fragments of real data (a genuine Social Security number from one person, a real address from another, a legitimate utility bill from a third) combined with AI-generated photographs, AI-written communications history, and deepfake video for live verification checks.
These profiles do not open accounts and immediately commit fraud. They build credit histories first. They receive direct deposits. They apply for small credit lines and pay them off. Over months or years, they become indistinguishable from genuine customers - until the moment the criminal behind them decides to extract maximum value. At that point, the account might be used to receive and forward stolen funds, take out a large loan with no intent to repay, or serve as a launchpad for further fraud using the accumulated trust score.
Cifas' assessment is explicit: personal instant and easy-access bank accounts saw a 455% rise in identity fraud filings in 2025, a 7,131-case increase. Basic banking products - the ones with the least friction, by design - are now prime targets because synthetic identity documents are sophisticated enough to pass their simplified checks.
"We anticipate more use of AI to personalise attacks and build credible, long-term profiles - reinforcing the need for cross-sector collaboration to spot patterns earlier." - Stephen Dalton, Director of Intelligence, Cifas, March 12, 2026
The deepfake dimension extends beyond document fraud. Account takeovers now frequently involve AI-generated voice and video in calls to bank customer service lines. A criminal who has obtained enough personal data about a target can generate a convincing voice clone of that person, call the bank, answer security questions in the target's voice, and request a password reset or address change. Cifas flags this as an accelerating threat in the account takeover section of the Fraudscape report, alongside credential stuffing attacks that use AI to automate millions of login attempts per hour against financial institutions.
The Proxy Network: Infrastructure for Hire
On March 13, 2026, Eurojust announced the takedown of what investigators described as a massive illicit IP proxy network used by cybercriminals to mask their digital presence during fraud operations. The coordinated operation spanned eight countries and was supported by Europol. The network was taken offline.
The technical architecture was significant. The network had silently infected approximately 369,000 consumer modems and home routers across 163 countries with malware, without the owners' knowledge. When a criminal needed to make an account creation request, a login attempt, or a fraudulent transaction appear to originate from a legitimate residential IP address in a specific country, they simply routed their traffic through one of these infected devices. The device owner had no idea.
Approximately 124,000 customers used this service, paying for access anonymously through a dedicated cryptocurrency platform. Total revenue generated for the network's administrators exceeded five million euros before the shutdown. The price point - roughly 40 euros per customer per operational use - made the service accessible to mid-tier fraud operations that could not afford to maintain their own residential proxy networks.
This is the broader ecosystem that the Cifas numbers reflect but do not fully capture: a mature underground economy of specialist services, each fulfilling a discrete function in the fraud supply chain. There are services that sell synthetic identity kits. Services that rent compromised residential IP addresses. Services that provide deepfake video generation for biometric bypasses. Services that manage and coordinate networks of money mules. Services that provide fraud-as-a-service scripts, complete with objection-handling guides for when a target becomes suspicious.
None of these services need to be run by the same criminal organization. They are modular. A small operation with minimal technical sophistication can assemble a professional-grade fraud capability by purchasing components off the shelf, the same way a startup purchases cloud infrastructure. The barrier to entry for large-scale financial fraud has collapsed.
Meta, Vienna, and the Industry Accord
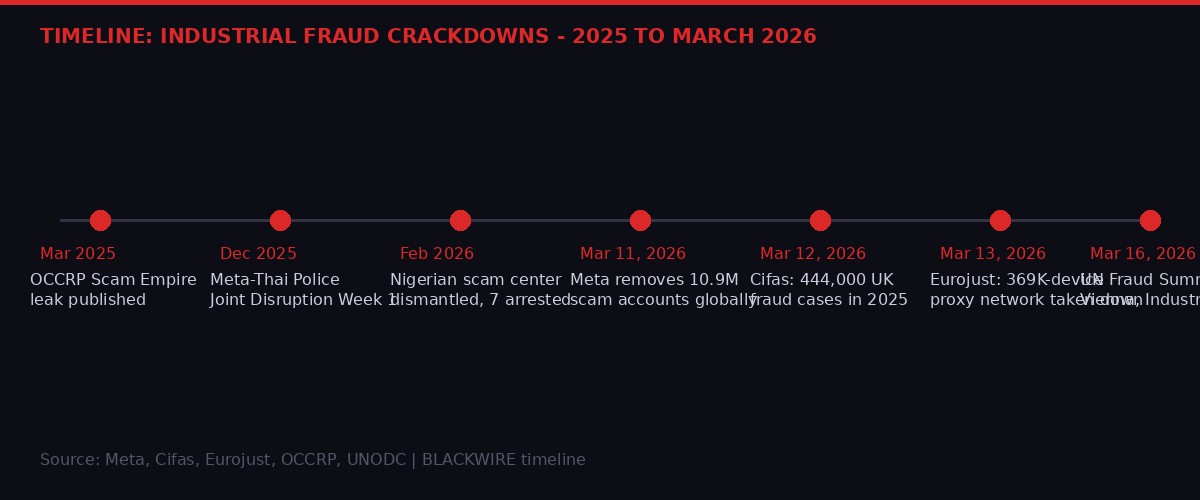
Timeline of key law enforcement and industry actions against industrial fraud operations, from OCCRP's Scam Empire investigation through the March 2026 UN Global Fraud Summit in Vienna. BLACKWIRE analysis.
On March 11, 2026, Meta published what it called an updated accounting of its anti-scam measures - a document that, read carefully, serves as both a progress report and an admission of the scale of the problem. The company removed 10.9 million accounts on Facebook and Instagram associated with criminal scam centers in 2025. It removed 159 million scam advertisements, 92% of which it caught before anyone reported them. It deployed AI tools to detect celebrity impersonation, synthetic media, and deceptive domain redirects.
These are genuinely large numbers. They are also a fraction of the total. Meta itself acknowledges in its Adversarial Threat Report that the industrialization of scams "continues to grow," and that each time the company develops a detection capability, criminal networks adapt. The 159 million scam ads removed implies that scam ad volume is measured in hundreds of millions per year - because the ones removed are not all of them, or even most of them.
The new tools Meta announced in March 2026 reflect this dynamic. WhatsApp device-linking warnings will now alert users when behavioral signals suggest a linking request is suspicious - because criminals have been tricking users into scanning QR codes that give them full access to WhatsApp accounts. Messenger will now deploy AI scam detection that warns users when a new contact exhibits patterns of common scam behavior. Facebook will test alerts when friend requests come from accounts with signs of suspicious activity.
These are reactive tools, built to address threats that have already been operating at scale. The romance scam infrastructure that Meta's Fraud Intelligence and Reciprocal Exchange (FIRE) team disrupted in early 2026 - 15,000 assets using fake profiles of Japanese women targeting older men - had been running long enough to generate substantial revenues before detection. The scam center in Nigeria that Meta helped dismantle had targeted British and American citizens for an extended period before the joint operation with the NCA and Nigerian Police landed seven arrests.
On March 16, 2026, at the United Nations Office on Drugs and Crime Global Fraud Summit in Vienna, Meta signed the Industry Accord Against Online Scams and Fraud alongside ten other major technology companies: Adobe, Amazon, Google, Levi's, LinkedIn, Match Group, Microsoft, OpenAI, Pinterest, and Target. The accord is voluntary. It commits signatories to share intelligence on scam activity, implement best practices for account verification, and coordinate on cross-platform enforcement.
"Scammers are growing more sophisticated, and they exploit gaps between companies and platforms - which is why tackling global online fraud demands a united, collective response." - Nathaniel Gleicher, Global Head of Counter Fraud, Meta, March 16, 2026
The accord is a genuine step forward in that it formalizes coordination that previously happened informally and inconsistently. But it is also, by design, non-binding. The companies signing it face no penalty for non-compliance and set no measurable targets. Its value will be determined entirely by what happens operationally after the Vienna meeting room clears out.
The Money Mule Economy: Who Gets Prosecuted
Here is where the mathematics of industrial fraud enforcement reveal their deepest problem. The individuals most likely to be prosecuted for their role in the fraud ecosystem are the mules - the people at the bottom of the supply chain, often recruited under false pretenses, processing funds on behalf of criminal networks they never met and whose structures they never understood.
A significant portion of convicted money mule cases involve people who genuinely believed they were employed in a legitimate financial processing role. Cifas data shows that 20% of people recruited into muling schemes did not know it was illegal. The recruitment pipelines have become sophisticated enough that the job offers are indistinguishable from genuine employment. There are fake websites, fake HR departments, and fake onboarding processes. The mule receives a contract, a "job description," and a small legitimate payment before the criminal proceeds begin flowing through their account.
The architects of these operations rarely get prosecuted because they are rarely reachable. They operate from jurisdictions with limited extradition treaties or failed state conditions. They use encrypted communications and rotate identities. When one fraud network is dismantled, the operators typically re-establish elsewhere within weeks, having already migrated the valuable components - the identity databases, the AI models, the customer lists - to new infrastructure.
NCA data cited in the Fraudscape report shows UK law enforcement fraud convictions rose 27% since 2022 - but this increase is almost entirely in low-level prosecutions. The structural organizers, the software developers who build the fraud-as-a-service toolkits, the money brokers who convert stolen funds into clean assets, the call center owners who operate the scam compounds - these individuals continue to operate largely without consequence.
The Older Victim Problem
Cifas data reveals a persistent and worsening demographic pattern: people over 61 are the most commonly targeted victims across nearly every fraud category. In identity fraud, victims over 61 account for 29% of filings - a 13% rise year on year. In account takeover, the same age group accounts for 31% of cases. The targeting is deliberate. Older individuals are more likely to have accumulated savings, less likely to have strong digital security hygiene, and more susceptible to social engineering tactics that exploit authority - impersonating banks, government agencies, or medical services.
The statistics on impersonation fraud deserve particular attention. Romance scams - of the type documented in OCCRP's investigation into a Nigerian man who allegedly posed as the Crown Prince of Dubai to extract $2.5 million from Romanian businesswomen - represent just the visible surface of a much larger impersonation economy. For every OCCRP investigation that ends in an arrest, there are thousands of operations that never come to light. A second victim of the same Dubai prince scammer came forward in Romania in March 2026, after watching the documentary about the first victim. The pattern was identical: LinkedIn contact, fake royal foundation, escalating financial requests, a "meeting" with a fraudulent financial manager in London.
The UK's Insurance Fraud Bureau has noted a 26% rise in motor insurance identity fraud cases in 2025 - a category that involves creating fake identities to purchase insurance, making fraudulent claims, and cycling the proceeds through the broader laundering infrastructure. The connection between insurance fraud and money laundering is tighter than most coverage suggests: fake insurance claims are one of the cleanest methods for converting criminal proceeds into documented payouts that appear entirely legitimate.
What Comes Next: The Arms Race Has No End
Cifas, Meta, Eurojust, and the NCA are all, in their own ways, describing the same structural problem. The legitimate economy has spent decades developing increasingly powerful digital tools to reduce friction - easier account opening, faster payments, more accessible credit. Criminal networks have spent the same period developing tools to exploit every point of that friction reduction. When banks made it easier to open a savings account online, criminals built synthetic identities that could pass the simplified checks. When social media platforms made it easier to build an audience, criminals built fake celebrity profiles to run investment scams. When messaging apps made cross-border communication seamless, criminal call centers relocated to the jurisdictions where they were hardest to reach.
The current generation of AI tools accelerates every step of this exploitation. Generative AI makes synthetic identities cheaper and more convincing. AI voice cloning makes social engineering phone calls more persuasive. AI-driven credential stuffing makes large-scale account takeover attempts faster and more targeted. Fraud-as-a-service platforms now offer AI-assisted script generation for fraud calls, real-time coaching for fraud operatives on how to handle resistant targets, and automated follow-up systems that maintain contact with thousands of potential victims simultaneously - far more than any human team could manage.
The response from technology companies and law enforcement is also increasingly AI-powered. Meta's celebrity impersonation detection, its domain impersonation scanning, its Messenger AI scam review - these are all machine-learning systems trained to detect patterns that human moderators cannot process at scale. Cifas and the NCA emphasize cross-sector data sharing as the key enforcement priority: the idea that patterns visible across multiple companies simultaneously - a synthetic identity used in banking, insurance, and telecoms within the same week - can trigger faster intervention than any single institution could manage alone.
The UN Global Fraud Summit's Industry Accord represents an attempt to institutionalize this cross-sector coordination at a global level. The UNODC's framework for multi-stakeholder collaboration, which Meta, Google, Microsoft, and their co-signatories endorsed in Vienna, creates at least a formal architecture for the kind of intelligence sharing that enforcement agencies have been requesting for years.
Whether it will matter depends on execution. Criminal networks do not sign accords. They do not wait for frameworks to be operationalized. They adapt in real time, pivoting from targeted platform defenses toward less-defended surfaces, migrating from one jurisdiction to another when enforcement pressure rises, and constantly recruiting new infrastructure - new mules, new proxy networks, new scam call center employees, many of whom were themselves initially trafficked or deceived into the work.
The 444,000 figure in the Cifas Fraudscape 2026 report is not a warning about where fraud is heading. It is a measurement of where fraud already arrived. The question the Vienna accord, the Meta enforcement announcements, and the NCA priority designations all leave unanswered is whether the pace of legitimate response can match the pace of criminal adaptation - or whether the industrialization of fraud has moved faster than any institutional response is capable of following.
TIMELINE: Industrial Fraud - Key Events, 2025-2026
Sources and Methodology
This investigation draws on the following primary sources: the Cifas Fraudscape 2026 report published March 12, 2026 (cifas.org.uk), including the full Fraudscape data portal at fraudscape.co.uk; Meta's anti-scam enforcement announcement published March 11 and updated March 16, 2026 (about.fb.com); the Eurojust announcement of the proxy network takedown published March 13, 2026 (eurojust.europa.eu); the OCCRP Scam Empire investigation published March 2025 and the March 16, 2026 follow-up on the Nigeria fake-prince arrest; the Industry Accord Against Online Scams and Fraud published at the UNODC Global Fraud Summit in Vienna on March 16, 2026; and the NCA's published statistics on UK fraud enforcement convictions.
Background context draws on previous OCCRP reporting on criminal call center networks in Southeast Asia, the Scam Empire leak, and Meta's Adversarial Threat Report for the first half of 2026. All statistics cited are sourced to the specific institutional reports in which they appear and have not been independently verified by BLACKWIRE. Where methodological caveats apply - particularly around Cifas member reporting practices and their effect on case counts - they are noted in the relevant sections.
BLACKWIRE is an independent investigations newsroom. We do not accept advertising from financial institutions, technology companies, or law enforcement agencies. We accept no editorial direction from sources. Corrections policy: errors reported to newsroom@blackwirenews.com will be acknowledged within 24 hours and corrected with a visible amendment notice.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram