Made in Europe, Dropped on Kyiv: How EU-Manufactured Chips Power Russia's Drone War
A new OCCRP investigation confirms what forensic analysts have documented since 2022: the Shahed drones dismantling Ukraine's power grid contain semiconductors from German, Dutch, Austrian, and American manufacturers. The supply chain runs through Istanbul, Dubai, and Almaty. Nobody has been prosecuted.

Graphic: BLACKWIRE / Based on OCCRP investigation "Made in the EU, Dropped on Kyiv" (February 18, 2026)
The drone that punched through an apartment block in Kharkiv on a Tuesday night last winter contained a microcontroller manufactured in Munich. The guidance system ran chips made at a fab in the Netherlands. The power regulation circuit board included a component traced back to a production line in Villach, Austria.
This is not a hypothetical or an isolated case. Engineers and forensic investigators sifting through drone wreckage across Ukrainian battlefields have documented this pattern hundreds of times since September 2022, when Russia first deployed the Iranian-designed Shahed-136 in mass. The evidence is in the rubble. The supply chain is documented. The companies named. The transit routes mapped.
And yet the flow of European-manufactured components into Russia's drone assembly lines continues.
On February 18, 2026, the Organized Crime and Corruption Reporting Project published its latest investigation into this sanctions evasion network, detailing how European parts - particularly from Austria-linked shell companies - continue reaching Russia's primary drone factory at Alabuga in Tatarstan. The investigation builds on years of documented evidence from Conflict Armament Research, the Ukrainian Prosecutor General's Office, and multiple national intelligence services. The conclusion remains the same: the EU's export control system is failing, and Russian drones are the proof.
The Weapon and Its Anatomy
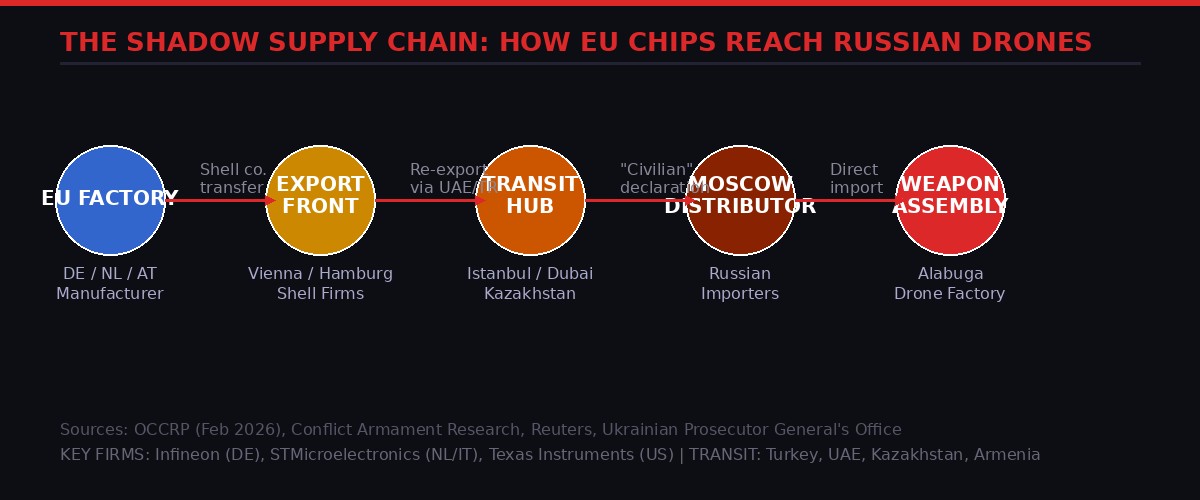
How EU-manufactured components travel from Western factories to Russian drone assembly. Source: OCCRP, CAR, BLACKWIRE analysis
The Shahed-136 - which Russia now assembles domestically under the designation Geran-2 - is not a sophisticated weapon. That is precisely what makes it so effective and so difficult to stop. It is a delta-wing loitering munition, essentially a flying bomb, packed with roughly 40 kilograms of explosive and guided to its target by GPS navigation. It costs an estimated $20,000 to $50,000 per unit to produce, a fraction of the cost of Western air defense interceptors.
What makes the Shahed lethal also makes it dependent on Western technology. The guidance systems, navigation computers, and power electronics require precision semiconductors that Russia cannot manufacture domestically at scale. Following international sanctions imposed after the 2022 invasion, Russian domestic chip production cannot supply the volumes needed for industrial-scale drone production.
Conflict Armament Research, a UK-based organization that forensically analyzes recovered weapons on active battlefields, has published multiple field dispatches documenting the component contents of Shahed variants recovered in Ukraine. Their analysis, cross-referenced with findings from Ukraine's Defense Intelligence Directorate, identifies a consistent set of manufacturers whose products appear across the drone's circuit boards.
Texas Instruments microcontrollers appear in the navigation computing systems. STMicroelectronics - whose fabs straddle the Netherlands, Italy, and France - provides power management ICs. Infineon Technologies, headquartered in Munich, contributes components to propulsion and guidance systems. TE Connectivity, registered in Switzerland, supplies connector components. NXP Semiconductors, headquartered in Eindhoven, has been found in recovered navigation boards.
All of these companies manufacture and export legally. None of them shipped these components directly to a Russian weapons factory. The question that investigators have spent three years trying to answer is: who did the shipping for them?
Key Finding: Component Persistence
Despite four EU sanctions packages and multiple export control tightening measures since 2022, CAR reports that "the proportion of Western-manufactured components in recovered Shahed units has not significantly decreased through 2025 and into 2026."
The components change - newer chip generations appear as older sanctioned ones become harder to source - but the supply continues. Russia is not running out of Western electronics.
Follow the Silicon: Inside the Evasion Network
The components leave their factories with legitimate export documentation. A batch of microcontrollers leaves an Infineon distributor in Munich bound, on paper, for a technology firm in Istanbul. The Istanbul firm - often registered weeks before the shipment, operating from a virtual office address, and sharing directors with a dozen other similar entities - holds the goods briefly, re-packages them, and ships them to a registered importer in Almaty, Kazakhstan. The Kazakhstani entity moves the cargo across the Russian border with documents describing it as "electronic components for industrial machinery."
This is the core architecture of the evasion network: multiple jurisdictional hops, each one stripping away the paper trail that would connect the original manufacturer to the end user. By the time the chip arrives in Tatarstan, its legal provenance is buried under layers of re-export documentation.
The OCCRP's February 2026 investigation adds new detail to this picture, focusing specifically on a cluster of Austria-registered trading companies that appear to have served as conduits in 2024 and 2025. The companies - identified in OCCRP reporting as operating from registered addresses in Vienna and Graz - had minimal public presence and thin corporate filings, but handled tens of millions of euros in electronic component transactions.
"The companies we identified were classic financial ghosts. No websites. No employees you could find. Directors registered to residential addresses. But the transaction records show them handling export volumes that would suggest a serious industrial operation." - OCCRP investigator, quoted in the February 2026 investigation
Austria presents a specific vulnerability in EU export control architecture. Unlike Germany, France, or the Netherlands - which maintain robust customs intelligence units with significant technical capacity - Austria's export licensing enforcement has historically been under-resourced relative to the volume of dual-use goods that transit through Vienna's position as a central European trade hub. The OCCRP findings indicate this gap has been exploited systematically.
Turkey remains the single most important transit jurisdiction. Reuters documented in 2023 that more than forty Turkish companies were identified as having shipped sanctioned goods to Russia after February 2022. Many of those companies dissolved and re-formed under new names after the investigation. The Turkish government, balancing its NATO membership against deep economic ties with Moscow, has repeatedly declined to implement the blanket re-export restrictions that Washington and Brussels have requested.
Kazakhstan presents a different but equally important vector. Sharing a border of more than 7,500 kilometers with Russia and lacking the institutional capacity for comprehensive customs enforcement, Kazakhstan has become the primary land route for electronics evasion. Trade statistics from Kazakhstan's National Statistics Bureau show dramatic surges in electronics imports from the EU and East Asia in the months following each new sanctions package - goods that do not correspond to Kazakhstan's domestic industrial capacity to absorb them.
Armenia and Georgia complete the picture of the former Soviet space serving as a sanctions laundry for Russian procurement. Western governments have applied increasing pressure on these countries, with some success: Armenian electronics exports to Russia dropped sharply following US secondary sanctions warnings in late 2024. But investigators note that as one route closes, the network adapts. The goods find new paths.
The Manufacturers' Defense - and Its Limits

Proportion of 200+ recovered Shahed drone units containing components from specific Western manufacturers. Sources: CAR field reports, OCCRP, Ukrainian Defence Intelligence
Every major manufacturer whose components have appeared in Russian weapons has issued a response following public reporting. The responses follow a remarkably consistent template.
They condemn Russia's invasion. They express commitment to compliance with export controls. They note that they cannot control the actions of their distributors or downstream customers after the point of sale. They cooperate, they say, with government investigations. They have "enhanced due diligence procedures." They have "terminated relationships" with identified distributors.
Infineon Technologies, whose components appear with particular frequency in CAR's forensic reports, told Reuters in 2023 that it had "implemented comprehensive measures to prevent the misuse of Infineon products" and had "terminated business relationships with identified distributors who violated export control regulations." The company noted that it sells to thousands of distributors globally and cannot monitor all downstream transactions.
This is technically accurate and simultaneously inadequate. The problem is structural, not a failure of individual compliance programs. Dual-use components - electronics that have both civilian and military applications - are the lifeblood of global manufacturing. They are sold in volumes of millions of units. They flow through distribution chains with dozens of intermediaries. No manufacturer can achieve full downstream visibility in this environment without fundamentally restructuring how the global electronics market operates.
But investigators argue that the manufacturers' posture is too passive. CAR and OCCRP both identify patterns that a proactive monitoring effort could detect: distributors in Turkey or UAE placing anomalously large orders for components with no plausible civilian end use; shipping addresses that resolve to vacant lots; companies incorporated weeks before large purchases. These are red flags that sophisticated compliance programs should catch - and sometimes demonstrably do not.
"We're not asking these companies to be intelligence agencies. We're asking them to do basic customer due diligence. When a newly-formed company in Istanbul orders 50,000 units of a navigation-grade microcontroller with no apparent business justification, that should trigger a question." - European Commission official, speaking on background, cited in OCCRP February 2026
There is also a financial incentive problem. The components in question are profitable, high-volume products. Tightening distribution controls has real costs - lost sales, slower order processing, friction with established trading relationships. Until the penalty for compliance failure clearly exceeds the revenue benefit from loose controls, the incentive structure does not favor tighter compliance.
The EU's Enforcement Machinery - And Its Gaps
Since February 2022, the European Union has adopted fourteen packages of sanctions against Russia. Each package has tightened export restrictions on dual-use items and added new goods to the prohibited list. The latest packages include explicit "no re-export to Russia" clauses and requirements for end-user certificates on sensitive technology exports to a list of high-risk third countries.
The legislative framework is, on paper, substantially stronger than it was four years ago. The enforcement reality is something else.
EU export control enforcement is, fundamentally, a member-state function. The Commission sets the rules; national customs and trade enforcement agencies implement them. This creates twenty-seven different enforcement regimes, with dramatically varying levels of resource, technical expertise, and institutional priority.
| Country | Export Control Agency | Known Prosecutions (2022-2026) | Assessment |
|---|---|---|---|
| Germany | BAFA (Federal Office for Economic Affairs) | 12+ cases | Most active enforcement; dedicated Russia task force |
| Netherlands | CDIU (Central Import/Export) | 8 cases | Strong; ASML incident raised profile significantly |
| France | SBDU (Service des Biens Duaux) | 5 cases | Moderate; resource constraints noted |
| Austria | BMAW (Ministry of Labour and Economy) | 1 case (pending) | Weak; OCCRP identifies as key vulnerability |
| Baltic States | National customs agencies | 7 combined | Improving rapidly; high political motivation |
Germany's BAFA - the Federal Office for Economic Affairs and Export Control - has been the most active enforcement agency, establishing a dedicated Russia task force and prosecuting multiple cases of sanctions evasion. But German investigations have repeatedly hit the same wall: by the time BAFA traces a component back through the distribution chain, the front companies responsible for the onward shipment have dissolved, the directors have scattered, and the beneficial ownership is buried in offshore structures.
The OCCRP investigation highlights Austria as the most acute current vulnerability. Austrian law enforcement has brought exactly one export control prosecution related to Russia since 2022, and that case remains pending. The Vienna-based companies identified in OCCRP's reporting operated for months before any regulatory attention reached them - and by the time investigators looked closely, several had already wound up their operations.
The Commission has pushed for greater coordination through a new "Export Control Coordination Group," established in 2024, and has proposed harmonized enforcement standards. Progress has been slow. Member states guard their sovereignty over trade enforcement jealously, and smaller states lack the political will and budget to match the enforcement capacity of Germany or the Netherlands.
A separate problem is intelligence sharing. The United States, which maintains the most comprehensive visibility into global sanctions evasion networks through Treasury's Office of Foreign Assets Control, has repeatedly provided European partners with specific intelligence on active evasion routes. European enforcement agencies report that acting on this intelligence is often frustratingly slow - requiring legal procedures, coordination across ministries, and cooperation from third-country governments that may not be forthcoming.
Ukraine's Infrastructure Under Fire - The Human Cost
What these bureaucratic failures mean in practice is written in rolling blackouts and frozen cities.
Russia's aerial campaign against Ukraine's energy infrastructure escalated sharply in the winter of 2024-2025 and has continued through 2026. The primary weapon is the Shahed drone - cheap enough to deploy in swarms, hard enough to intercept en masse, and precisely accurate enough to strike transformer stations, substations, and power generation facilities.
Ukraine's Energy Ministry reported that Russian drone and missile strikes destroyed or severely damaged more than 40 percent of the country's total electricity generation capacity over the 2024-2025 winter season. Kharkiv, a city of 1.4 million in eastern Ukraine, experienced rolling blackouts of up to 18 hours per day during the coldest months. Kyiv's hospitals operated on generator power for extended periods. Water treatment plants lost power, creating public health emergencies in multiple cities.
The repair cost for Ukraine's energy infrastructure, as estimated by the World Bank and Ukraine's Ministry of Economy, exceeded $14 billion by the end of 2025. International donors have contributed reconstruction funds. Those same donors' countries manufacture the chips that make the weapons doing the destroying.
"Every time I see a report about a new EU sanctions package, I think about the substations we've lost. The packages keep coming. So do the drones. Something in that equation is broken." - Senior official, Ukraine's Ministry of Energy, speaking to Reuters, February 2026
Ukrainian forensic teams have developed considerable expertise in component analysis. The State Bureau of Investigations and the Prosecutor General's Office maintain detailed databases of components recovered from drone wreckage, cross-referenced with batch numbers, distributor codes, and export documentation where available. This evidence has been shared with European partners - and has formed the evidentiary basis for several of the export control prosecutions that have moved forward in Germany and the Netherlands.
But the process is slow. By the time a recovered chip is traced through the distribution chain to an identifiable exporter, the exporter has often restructured or dissolved. The prosecution of individual cases does not disrupt the network; it educates it about which operational security lapses to avoid.
The Transit Country Problem: Closing the Net
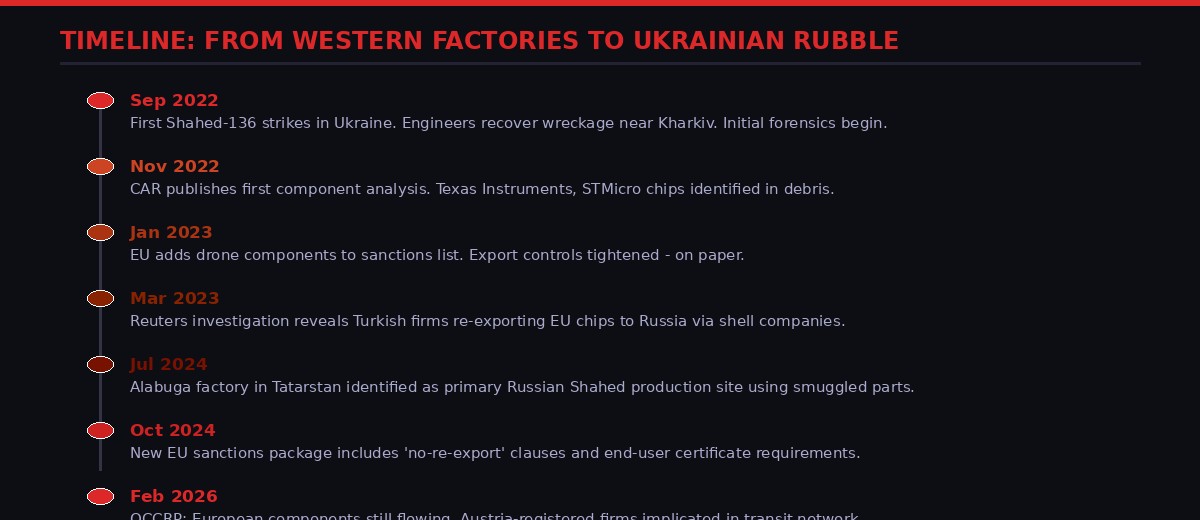
Key events in the documentation and failed containment of EU semiconductor components in Russian weapons systems, 2022-2026
The fundamental challenge of sanctions enforcement in this domain is that it requires the cooperation of countries that have their own interests. Turkey, Kazakhstan, the UAE, and Armenia are not adversaries of the West - but they are not willing to absorb the economic costs of full compliance with Western sanctions regimes that they did not choose.
Turkey's position is the most complex. As a NATO member, Turkey is formally aligned with the alliance that is supporting Ukraine. Turkish officials have made periodic gestures toward tighter export controls. But Turkey's trade relationship with Russia is substantial - bilateral trade volumes actually increased in 2022 and 2023, as Turkey became a key channel for goods Russia could no longer source from Western suppliers directly. The Turkish electronics export sector has been a direct beneficiary of this role.
The United States has applied increasing pressure through secondary sanctions threats - the warning that entities doing sanctions-busting business with Russia may face exclusion from the US financial system. This has been effective with larger Turkish firms that have significant US exposure. It has been less effective with the smaller, rapidly-cycling front companies that do the actual movement of goods.
Kazakhstan's government has made more explicit commitments to restrict re-export of sanctioned goods, following direct pressure from Washington and Brussels in 2024. Kazakh customs data shows the transit volumes have declined - but investigators note that some of the decline reflects better statistical concealment rather than reduced actual flows. Goods that once moved under electronics categories now move under opaque industrial machinery classifications.
The UAE has been the most resistant to pressure. Dubai's role as a global trade hub, and the emirate's deliberate positioning as a sanctions-neutral financial and logistics center, makes it both economically vital and politically resistant to Western enforcement demands. OFAC has designated several UAE-based entities involved in Russian procurement, with limited effect on the broader network.
What investigators consistently find is that the evasion network has redundancy built in. When one route is closed, traffic redistributes to others. When front companies in one jurisdiction attract scrutiny, new companies form in others. The network is not a single pipeline that can be cut - it is a fluid system that finds new channels.
The Alabuga Connection
Russia's primary Shahed assembly facility, located in Alabuga Special Economic Zone in Tatarstan, is believed to produce between 300 and 500 drones per month at full capacity. Western intelligence assessments cited by Reuters and Bloomberg estimate that sustaining this production requires ongoing access to approximately 50,000 Western-manufactured electronic components per month.
Alabuga has been the subject of EU and US sanctions targeting its parent entities, but the facility itself continues operating. The components keep arriving. Analysts note that Russia has also invested heavily in domestic chip production at Mikron and Angstrem, but domestic capacity remains insufficient for the precision components required in guidance systems.
What Would Actually Work
Investigators, policy analysts, and former enforcement officials are not short of ideas about what a more effective response would look like. The problem is political will and institutional coordination, not analytical insight.
The most frequently cited reform is a shift from a "prohibited list" model to a "permitted end-use" model for the highest-risk component categories. Under current EU rules, dual-use goods can be exported freely unless they appear on a prohibited list - and maintaining that list's relevance against a fast-moving evasion network is an inherently reactive, losing battle. A permitted end-use model would flip the burden: exporters of specified high-sensitivity components would need to affirmatively demonstrate a legitimate civilian end use, rather than regulators having to prove a prohibited one.
Germany's BAFA has moved partially in this direction for certain chip categories, requiring enhanced end-user certification and post-shipment verification for the highest-risk component types. Early results suggest this reduces the volume of problematic exports, though it also increases compliance costs and friction for legitimate exporters.
A second reform is extraterritorial reach - the use of US-style secondary sanctions to deter third-country entities from participating in evasion networks. The EU has historically been reluctant to adopt the extraterritorial approach, viewing it as an overreach that could damage relationships with non-EU trading partners. The evidence that voluntary compliance is not working is pushing Brussels toward a harder position, but legislative progress is slow.
A third element is mandatory transaction monitoring for distributors of dual-use goods, similar to the Know Your Customer obligations that financial institutions carry. This would require distributors to maintain records of downstream customers and flag anomalous purchasing patterns to national authorities. Industry groups have resisted this on cost and competitive grounds, but the proposal is gaining traction in Commission discussions.
None of these reforms have been fully implemented. In the meantime, the February 2026 OCCRP investigation documents Austria-linked shell companies that operated for months, moving millions of euros in components, before anyone looked closely at them. By the time investigators looked, several had dissolved.
The drones keep flying. The lights in Kharkiv keep going out. And somewhere in the wreckage, there is another chip with a European manufacturer's mark on it, waiting to be logged in a database that may eventually, someday, lead to a prosecution.
Or it may not. The network has proven more durable than any individual attempt to close it. What the OCCRP investigation makes clear - what three years of forensic analysis, national prosecutions, and legislative packages have not changed - is that the European Union's component manufacturers are, despite themselves, co-producing the weapon dismantling Ukrainian infrastructure. The supply chain is documented. The transit routes are mapped. The companies are named.
The question is no longer what is happening. The question is whether anyone in a position to stop it will be held accountable for failing to do so.
What OCCRP's Investigation Found (Feb 18, 2026)
- Austria-registered shell companies identified as active transit points for EU chip exports to Russia in 2024-2025
- Components traced to Shahed drone assembly at Alabuga facility in Tatarstan
- Austrian enforcement: 1 pending prosecution in four years
- Network uses nested re-export chains averaging 4-6 jurisdictional hops
- New EU sanctions packages correlated with temporary route disruption, followed by adaptation within 60-90 days
- Manufacturers contacted; all declined to confirm or deny specific distributor relationships in the reported network
- September 2022 Russia deploys Shahed-136 in mass attacks on Ukrainian infrastructure. Engineers recover wreckage; component analysis begins.
- November 2022 Conflict Armament Research publishes first systematic component analysis identifying Texas Instruments, STMicro, and Infineon parts in recovered drones.
- January 2023 EU adds drone components to sanctions list. Additional export restrictions placed on 50+ electronic component categories.
- March 2023 Reuters documents Turkish front companies re-exporting EU chips to Russia. Forty-plus companies identified. Most dissolve within weeks of publication.
- October 2023 US Treasury designates UAE-based entities in Russian procurement network. Limited disruption; new companies form within months.
- July 2024 Alabuga factory formally identified by Western intelligence as Russia's primary Shahed production site. Component imports traced to sustained Western supply chain.
- October 2024 EU 14th sanctions package introduces "no re-export" clauses and enhanced end-user certificate requirements for high-risk third countries.
- February 2026 OCCRP investigation documents Austria as active evasion hub. Vienna-linked shell companies identified. Network operational and adapting.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram