DarkSword: The iPhone Exploit Russia Left in Plain Sight
Russian state-sponsored hackers deployed a six-vulnerability iOS exploit chain capable of silently compromising hundreds of millions of iPhones - then left the entire toolkit, completely undisguised and fully commented, sitting on publicly accessible Ukrainian websites for anyone to grab and reuse.

On March 19, 2026, researchers at Google Threat Intelligence Group, iVerify, and Lookout jointly disclosed the discovery of a sophisticated iOS exploit chain they call DarkSword. The tool had been in active deployment since at least November 2025, used by at least three distinct threat actor clusters across four countries. It exploits six separate vulnerabilities to fully compromise iPhones running iOS 18.4 through iOS 18.7 - versions that, as of early March 2026, still accounted for roughly a quarter of all iPhones in circulation.
That alone makes DarkSword a major story. But the detail that elevates it from "serious threat" to "watershed moment in mobile security" is this: the Russian spy group that deployed DarkSword left the entire exploit kit - complete source code, inline comments in English explaining every component, debug logging functions, and even the tool's own name - sitting on compromised Ukrainian websites with no obfuscation and no access controls. Anyone who visited the right URL and knew what they were looking at could download a working iPhone zero-day.
"It's all nicely documented, also. It's really too easy," said Matthias Frielingsdorf, iVerify cofounder and researcher who found the exploit. "Anyone who manually grabbed all the different parts of the exploit could put them onto their own web server and start infecting phones."
What DarkSword Actually Does
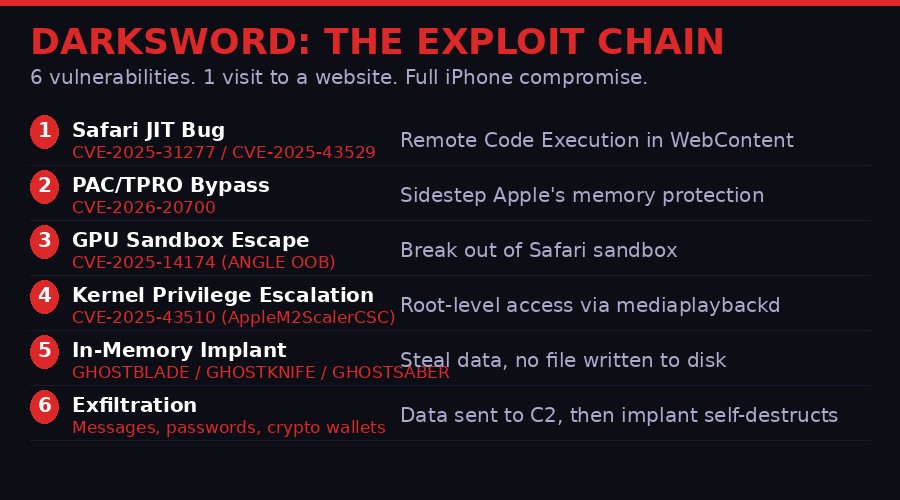
DarkSword is a "watering hole" attack. The victim doesn't click a malicious link, doesn't install anything, doesn't grant any permissions. They simply visit a website - a Ukrainian news outlet, a government portal - that has been compromised to serve a single invisible iframe. That iframe triggers a chain of six exploits that, within minutes, extracts every sensitive piece of data from the phone and deletes its own traces.
The chain is built entirely in JavaScript. There are no binary executables, no native code injected into the filesystem, no persistent backdoor installed. This is deliberately "fileless" malware applied to a mobile device - a technique normally associated with sophisticated Windows attacks.
Stage 1: Breaking Out of Safari
The attack begins with a vulnerability in JavaScriptCore, the JavaScript engine that powers Safari. DarkSword uses one of two bugs depending on the iOS version being targeted. Against iOS 18.4-18.5, it exploits CVE-2025-31277, a JIT RegExp match vulnerability that causes type confusion and allows attackers to read and write arbitrary memory locations. Against iOS 18.6-18.6.2, it switches to CVE-2025-43529, a use-after-free vulnerability in the JIT StoreBarrierInsertionPhase component.
Both bugs ultimately deliver the same capability: arbitrary memory read/write primitives within the Safari WebContent process. This gives attackers a foothold inside the browser sandbox, but Safari's isolation is only the first wall to breach.
Stage 2: Bypassing Apple's Memory Defenses
Modern iPhones run multiple layers of memory protection designed to prevent exactly this kind of exploitation. Pointer Authentication Codes (PAC) cryptographically sign memory pointers so that attackers who manage to corrupt memory can't redirect program execution. Trusted Path Read-Only (TPRO) prevents modification of certain critical memory regions. The JIT Cage restricts where JIT-compiled JavaScript code can execute.
DarkSword bypasses all of them in one step using CVE-2026-20700 - a vulnerability in dyld, Apple's dynamic linker. The researchers found that sensitive internal dyld structures are located in writable, unprotected stack memory. By abusing these structures, attackers can manipulate thread state to achieve arbitrary code execution despite PAC and TPRO being active. According to iVerify's technical writeup, this bypass was effective across all targeted iOS versions and represents a fundamental design flaw rather than a simple coding error.
Stage 3: Escaping the Sandbox via the GPU
With code execution established in Safari's WebContent process, the attacker still can't access the rest of the phone. WebContent runs in a strict sandbox that prevents it from touching user data, the filesystem, or other applications. To break out, DarkSword uses an unexpected vector: the GPU.
CVE-2025-14174 is an out-of-bounds write vulnerability in ANGLE, a graphics compatibility layer used by Safari's GPU process. By exploiting this alongside the same PAC bypass technique from Stage 2, attackers gain arbitrary memory read/write and function call capabilities inside the GPU process - which has significantly broader system permissions than the WebContent sandbox.
From the GPU process, the attack pivots again. Using selector 1 of the AppleM2ScalerCSCDriver kernel driver (CVE-2025-43510), attackers trigger a Copy-On-Write vulnerability that establishes arbitrary memory access inside mediaplaybackd - a system daemon that handles media playback and has access to the device's microphone, camera, and broad file system areas.
Stage 4: Kernel Privilege Escalation
The final technical hurdle is escalating from mediaplaybackd's process context to full kernel access. DarkSword achieves this by loading the JavaScriptCore framework directly into the mediaplaybackd daemon - an unusual technique that allows JavaScript code to run with daemon-level permissions. A final JavaScript module (/pe_main.js) then executes the kernel privilege escalation, giving attackers arbitrary read/write access to the iOS kernel itself.
At this point, the device is fully compromised. The attackers have root-equivalent access to everything on the phone.
Stage 5: Silent Data Exfiltration
The final stage deploys one of three JavaScript implants across multiple system processes. The three malware families - GHOSTBLADE, GHOSTKNIFE, and GHOSTSABER - were each used by different threat actor clusters and have different capabilities, but all share the same core "smash-and-grab" architecture.
DarkSword targets iOS 18.4 through 18.7 - versions that still account for approximately 25% of all iPhones worldwide as of March 2026, representing roughly 250-300 million devices. iOS 26.x users who have not updated to 26.3 may also remain vulnerable to some components of the chain.
The Three Ghost Malware Families

Google Threat Intelligence Group identified three distinct malware families deployed after a successful DarkSword compromise, each customized for different operator groups but sharing the same underlying exploit chain.
GHOSTKNIFE - The Russian Spy Tool
GHOSTKNIFE is the most thoroughly documented of the three, deployed by a group Google tracks as UNC6748 and later reused by the Russian state-sponsored group UNC6353. Written entirely in JavaScript, it operates as a modular surveillance platform rather than a simple data thief.
The implant's capabilities, as documented in Google's technical analysis, include: extraction of signed-in account tokens; complete message history from iMessage, WhatsApp, and Telegram; browser history and cookies; location history and GPS logs; photo library contents; calendar and notes data; live audio recording via the device microphone; file downloads from a command-and-control server; and screenshot capture.
Notably, GHOSTKNIFE also steals cryptocurrency wallet credentials - private keys, seed phrases, and authentication tokens for crypto applications. For an espionage tool targeting Ukrainian journalists and government officials, the inclusion of crypto theft capability is telling. It suggests the malware was either repurposed from criminal infrastructure, or that the operators ran a side business harvesting financial credentials from their espionage targets.
GHOSTKNIFE communicates with its command-and-control server using a custom binary protocol over HTTP, encrypted with a scheme based on ECDH (Elliptic-Curve Diffie-Hellman) key exchange and AES. The implant actively covers its tracks - one of its modules periodically deletes crash logs from /var/mobile/Library/Logs/CrashReporter/ to prevent forensic analysis.
"Instead of using a spyware payload to brute force your way through the file system - which leaves tons of artifacts of exploitation that are pretty easy to detect - this just uses system processes the way they're meant to be used. And it leaves far fewer traces." - Rocky Cole, CEO and cofounder of iVerify
GHOSTSABER - The Commercial Surveillance Version
The Turkish commercial surveillance firm PARS Defense used DarkSword to deploy a different implant: GHOSTSABER. This variant was observed in late November 2025 targeting users in Turkey, and again in January 2026 in a campaign against targets in Malaysia - suggesting that PARS Defense sells access to clients in multiple countries.
Unlike the relatively crude UNC6748 deployment, PARS Defense implemented the DarkSword loader with professional-grade OPSEC. Their version applied obfuscation to the exploit code and used ECDH and AES encryption for all communications between the infected device and the command-and-control server, hiding the exploit chain from network monitoring. They also correctly handled iOS version detection - loading the appropriate RCE exploit for each device version rather than using a fallback that ignored version entirely, as UNC6748's sloppy implementation did.
The involvement of PARS Defense is significant because it demonstrates a key dynamic in the iPhone exploit market: the same underlying exploit chain was simultaneously available to a Russian state intelligence service and a for-profit commercial surveillance vendor selling to multiple national clients. These are no longer separate threat landscapes.
The Broker Market and Operation Zero

Nobody knows with certainty who wrote DarkSword. The code itself offers clues: the main exploit stages contain detailed English-language comments with the DarkSword name embedded (const TAG = "DarkSword-WIFI-DUMP"), suggesting it was written by one team and sold or licensed to others with documentation included. The early-stage delivery scripts contain comments written in Russian, suggesting those wrapper components were adapted by a Russian-speaking operator.
The strongest circumstantial evidence points toward the exploit broker ecosystem centered around Russian firm Operation Zero. This connection threads through the DarkSword story and its predecessor, Coruna, in a way that illuminates how the iPhone zero-day market actually functions.
As TechCrunch reported in early March 2026, the Coruna exploit kit - a different iOS exploit chain used by UNC6353 in earlier campaigns against Ukraine - was created by Trenchant, a subsidiary of US defense contractor L3Harris that builds hacking tools for the US government. A former Trenchant employee, Peter Williams, pleaded guilty last year to stealing the company's tools and selling them to Operation Zero, a Russian broker firm that was subsequently sanctioned by the US Treasury Department.
Operation Zero then resold those tools to Russian state-sponsored hacking groups and apparently to other buyers. DarkSword's deployment by both Russian intelligence (UNC6353) and PARS Defense - a Turkish commercial surveillance vendor serving multiple national clients - fits the same distribution pattern. Whether DarkSword originated from US government contractor tools or was independently developed remains unknown, but the broker market ensures it reaches whoever pays.
"If this one gets burned, I'll just go get another one. They know there's more where this came from." - Rocky Cole, iVerify CEO, describing the apparent mindset of the Russian operators who carelessly exposed DarkSword
The OPSEC Catastrophe That Changed Everything

State-sponsored hacking tools typically live behind carefully maintained walls. When Pegasus - NSO Group's iPhone spyware - was exposed in 2021, it had operated covertly for years, used only against precisely selected high-value targets. The same pattern held for most government-grade iPhone exploits discovered before 2025: used sparingly, against specific individuals, in ways designed to minimize detection and extend the operational lifespan of the underlying vulnerability.
DarkSword represents a rupture in that model.
The Russian group UNC6353 embedded DarkSword in compromised legitimate Ukrainian websites - news outlets and a government portal at 7aac.gov.ua - to hit anyone visiting those sites, not just specific targets. No longer surgical; now a net designed to catch anyone who clicked the wrong link. Then they left the complete exploit chain - all six stages, with no obfuscation, with debug logging functions, with explanatory comments - accessible to any researcher or rival intelligence service who found the right URL.
Frielingsdorf and his team at iVerify did exactly that. "We tracked the URL to two Ukrainian websites hosting a malicious iframe," they wrote. Following the infrastructure, they recovered the complete DarkSword kit. The carelessness wasn't accidental negligence - it reflects a deliberate shift in doctrine.
The working theory among researchers: Operation Zero or a similar broker is selling access to exploits at scale. When state actors treat zero-days as cheap, disposable commodities rather than precious intelligence assets, they stop taking precautions to preserve them. Use it, burn it, buy another one. The broker market has made individual zero-days cheap enough that operational security around them no longer seems worth the effort.
The second-order consequence is predictable and alarming. By leaving DarkSword publicly accessible, the Russian operators effectively donated a fully-functional iPhone exploit kit to every other threat actor on the internet. Cybercriminal groups, other state intelligence services, smaller surveillance vendors - all can now grab and deploy DarkSword against their own targets.
"We know there's more where this came from," Cole says. That's the real message the Russian operators are sending, whether intentionally or not. The commodity zero-day market is deep enough that burning one tool by exposing it recklessly doesn't feel like a loss anymore.
The Vulnerability Timeline: Six CVEs, Multiple Patches
Apple patched the six DarkSword vulnerabilities across multiple iOS releases between July 2025 and February 2026. Google Threat Intelligence Group reported the vulnerabilities to Apple in late 2025, and by the release of iOS 26.3 in February 2026, all six were addressed.
| CVE | Component | Type | Patched In | ITW? |
|---|---|---|---|---|
| CVE-2025-31277 | JavaScriptCore JIT (iOS 18.4) | Type confusion | iOS 18.6 | No |
| CVE-2025-43529 | JavaScriptCore JIT (iOS 18.6) | Use-after-free | iOS 26.2 / 18.7.3 | Yes |
| CVE-2026-20700 | dyld PAC/TPRO bypass | Design flaw | iOS 26.3 | Yes |
| CVE-2025-14174 | ANGLE GPU (sandbox escape) | Out-of-bounds write | iOS 26.2 / 18.7.3 | Yes |
| CVE-2025-43510 | AppleM2ScalerCSCDriver | Copy-On-Write | iOS 26.1 / 18.7.2 | No |
| Kernel LPE | XNU kernel | Privilege escalation | iOS 26.3 | Yes |
The timeline reveals something important: three of the six CVEs were exploited "in the wild" before Apple patched them. That means attackers were actively using these vulnerabilities against real targets while Apple's engineers were still working to close the holes. For the most critical component - the PAC/TPRO bypass in dyld - a patch didn't land until iOS 26.3, released February 11, 2026, even though the vulnerability was present and being exploited since at least November 2025. That's roughly a three-month window of active exploitation against a patched-but-not-all-updated userbase.
Apple has issued emergency patches for older devices that cannot run iOS 26, pushing fixes for some of these vulnerabilities to iOS 18.7.x. But not all devices are eligible for those updates, and millions of users have still not applied them.
Why This Matters More Than Previous iPhone Hacks

The cybersecurity community has tracked iPhone zero-day exploits for years. What makes DarkSword different - what elevates it above another line in a CVE database - is what it signals about the structural transformation of the mobile threat landscape.
From Scalpel to Shotgun
Previous iPhone exploits that made international headlines - Pegasus, ForcedEntry, BLASTPASS - were used with extraordinary restraint. Pegasus infections were counted in the dozens or hundreds of verified cases. ForcedEntry targeted specific journalists and activists by sending iMessages to their exact phone numbers. These tools were treated like nuclear weapons: enormously powerful, but too valuable to use recklessly.
DarkSword was embedded in websites serving broad Ukrainian audiences. The infection vector was "visit a Ukrainian news site while in Ukraine." Not "be a specific dissident." Not "receive a specially crafted message from a known operative." Just: be in Ukraine and read the news. That shift from surgical to indiscriminate represents a fundamental change in how state actors are using iPhone zero-days.
The Proliferation Problem
Even more troubling is the multi-actor proliferation Google documented. DarkSword was used by at least three distinct clusters - UNC6748 (possibly a broker customer), UNC6353 (Russian state espionage), and PARS Defense (Turkish commercial surveillance) - in campaigns across Saudi Arabia, Turkey, Malaysia, and Ukraine. The same exploit chain was simultaneously a tool of Russian intelligence and a commercial product available to any government willing to pay PARS Defense's rates.
"The back-to-back appearance of two different, powerful iPhone hacking techniques, possibly both sold by a broker firm with little discretion, suggests an increasingly active market for the resale of exploits," Wired's Andy Greenberg wrote in his report on the findings.
Operation Zero's business model - buying exploits from sources including compromised insiders at US defense contractors, then reselling to multiple nation-state customers without apparent vetting - means that a tool created for US government use could end up in the hands of Russian, Turkish, and Saudi intelligence services simultaneously. The sanctioned status of Operation Zero did not interrupt this trade.
iOS 26's Adoption Problem
There's a secondary angle here that Apple would prefer not to discuss: iOS 26 has an adoption problem that directly affects the security of hundreds of millions of users.
Apple redesigned iOS 26 with a controversial "liquid glass" interface that many users have found overly animated, difficult to read, and generally unpleasant. According to both Apple's own developer statistics and StatCounter data cited in the DarkSword disclosures, approximately 25% of iPhones were still running iOS 18.x as of late February 2026. That represents an enormous pool of devices that are, by definition, vulnerable to DarkSword in some form.
When users refuse to upgrade due to aesthetic changes they dislike, the downstream security consequences fall on everyone. The researchers are explicit: the population of iOS 18.x users is so large that even indiscriminate watering hole attacks can reach high-value targets simply through statistical probability. "A vast number of iOS users could have all of their personal data stolen simply for visiting a popular website," said Cole.
What You Should Do Right Now

DarkSword is patched in iOS 26.3. The actionable guidance from the research teams is clear and worth restating bluntly:
Update now. Go to Settings - General - Software Update. If you're running iOS 18.x, update to the latest available version. If your device can run iOS 26, update to iOS 26.3 or later. This closes all six DarkSword vulnerabilities and the Coruna vulnerabilities disclosed earlier this month. Apple issued emergency patches for older devices that cannot run iOS 26, pushing fixes into the iOS 18.7.x branch.
Enable Lockdown Mode if you are at elevated risk. Lockdown Mode, available in Settings - Privacy and Security, significantly hardens iOS against exploit chains like DarkSword by restricting JIT JavaScript compilation, blocking certain message attachment types, and preventing unusual device connections. It breaks some functionality, but for journalists, activists, government officials, or anyone with reason to believe they may be specifically targeted, the security benefit outweighs the inconvenience.
Check for compromise. Both iVerify and Lookout offer security applications that can detect the indicators of compromise associated with DarkSword. If you visited Ukrainian news sites or government portals in recent months while running iOS 18.x, a check is worthwhile. DarkSword's fileless, no-persistence design means it doesn't leave obvious artifacts, but it does leave some forensic trace in unified system logs.
The Timeline: How DarkSword Unfolded
The Bigger Picture: A Market That Can't Be Sanctioned Away

Two weeks before DarkSword's disclosure, the security community was digesting the Coruna iPhone toolkit - built by a US defense contractor, stolen by an insider, sold to Russia via Operation Zero. Now DarkSword adds a second, simultaneous exploit chain deployed by the same Russian spy group and the same commercial surveillance ecosystem. These aren't isolated incidents. This is a market operating continuously.
Operation Zero remains under US Treasury sanctions. Those sanctions have not stopped the firm from facilitating the sale of US-origin exploit tools to Russia. They have not stopped the proliferation of those tools to commercial surveillance vendors. They have not stopped the indiscriminate deployment of iPhone zero-days against civilian populations. Sanctions are a statement about values. They are not a technical barrier.
The deeper problem is structural. Governments - including the US government - fund the development of zero-day exploits as offensive tools. Those tools are developed by private contractors with employee turnover, insider threats, and inadequate handling procedures. They leak. They get stolen. They get resold. They end up simultaneously in the hands of a Russian FSB-linked spy group and a Turkish firm selling surveillance to Malaysia. The supply chain for iPhone zero-days runs directly through the US defense industrial base, and that supply chain is leaking at both ends.
Justin Albrecht from Lookout put it plainly: "People assumed that it was just going to be journalists or activists or maybe an opposition politician that was targeted, and that this wasn't a concern for a normal citizen. Now that we see iOS exploits being delivered through an unscrupulous broker, there's a whole market here for this to get to cybercriminals who will use it with far less discretion."
DarkSword is patched. The six CVEs are closed. Apple was fast once the full chain was disclosed. None of that changes the underlying reality: there are almost certainly other active exploit chains targeting iOS right now, in the hands of the same broker ecosystem, waiting to be discovered - or not discovered - as the next campaign unfolds.
The name DarkSword came from a single line in the WiFi password extraction module: const TAG = "DarkSword-WIFI-DUMP". The developers named their tool and documented it carefully - not for operational security, but because they expected it to be sold, used, and maintained by multiple teams across multiple deployments. It was a product, not a secret. That's the world iPhone users now inhabit.
Get BLACKWIRE reports first.
Breaking news, investigations, and analysis - straight to your phone.
Join @blackwirenews on Telegram